Abstract
IT resource planning contingency is key to curbing disruptions that result from various issues. Many firms are spending a lot of money to ensure that their computer systems are protected from interruptions. With regard to IT resource contingency plans, organizations should prepare adequately to deal with emergencies. Seven steps are involved in IT contingency planning. It is important to note that each stage plays unique roles.
Introduction
Information technology (IT) is a vital element in the running of business establishments. IT provides computerized systems that are essential for efficient and effective management of organizations’ affairs without interruptions (Cerullo & Cerullo, 2004).
According to Cerullo and Cerullo (2004), contingency planning entails putting in place plans, methods, and technical measures that would help a system to work efficiently, especially when there is a disaster or an interruption. It focuses on increasing performance outcomes. However, IT systems are vulnerable to many disruptions, which can be reduced or eliminated. Such a plan is essential in exploring and preparing for emergencies.
This is for the reason that it has procedures that should be followed in the event that disasters occur (Cerullo & Cerullo, 2004). It is vital in assisting IT systems to be effective when storing and retrieving data. In fact, changing the location of IT systems and retrieving IT functions that utilize substituted tools are short-term measures that would be important in promoting the effectiveness of firms (Swanson, 2011).
Therefore, with an increased number of cases that requires adequate preparation in the IT world, contingency planning becomes vital. This paper focuses on discussing issues and procedures that are involved in IT resource contingency planning. In addition, it highlights the recommendations of planning in relation to IT resources.
Statement of the problem
High-quality goods and services are not only essential for improving health outcomes, but also a right for every citizen in a country. High-quality goods and services will only be provided if organizations utilize IT, which is key to the success of a business in a competitive business world (Swanson, 2011).
This is because many activities can be performed digitally using modern technological platforms. Organizations focus on emerging technologies as the best solutions with regard to the provision of better services and production of high-quality goods (Swanson, 2011). To achieve these objectives, many companies utilize IT systems to assist them in data storage and retrieval (Swanson, 2011).
Many firms employ IT for the efficient and effective performance of tasks. In addition, IT helps organizations to save time and reduce costs in relation to labor. Swanson (2011) argues that in the modern world, IT is considered instrumental in administration of firms, but for it to be effective, there must be preparations for contingencies in IT resources.
It is evident that IT employment has made firms quality-oriented, making them produce excellent outcomes in the business environment (Swanson, 2011). Therefore, IT system contingencies should be planned to facilitate improvement in firms. Notably, IT systems have experienced failures due to power shortages and defects, rendering them unreliable (Stoneburner, Goguen & Feringa, 2002). In view of this, there is an urgent need to plan for IT resource contingencies.
Issues in IT resource contingency planning
For effective and efficient application of IT in companies, there is a need to plan adequately to prepare IT resources to mitigate errors that could result from emergencies, such as power losses and other defects (Stoneburner et al., 2002). Moreover, it is important to understand that it would require adequate preparation.
The first issue that would require planning is the disruption that would be caused by power losses (Stoneburner et al., 2002). Notably, when using IT devices, electricity is essential. In cases of losses, data are lost, especially when they have not been saved.
Thus, it is prudent to prepare in order to reduce data losses in cases where power is disrupted. Another issue with regard to IT resource contingency planning is risk assessment (Stoneburner et al., 2002). This involves examining a threat that would affect performance outcomes of an organization before it negatively impacts it (Stoneburner et al., 2002).
This measure aims at protecting an IT system from natural, human, and environmental problems. According Stoneburner and colleagues (2002), poor motivation is an issue that impacts contingency planning negatively in the IT sector. It is clear that this type of preparation is considered as plan B (an alternative) and, in most cases, priorities are given to plan A, which offers the required outcomes immediately (Stoneburner et al., 2002).
Moreover, personnel within a firm, including managers, system administrators, information system security officers, system engineers, and architects, are vital in preparing when utilizing IT resources (Stoneburner et al., 2002). They are the ones who give commands to computers to perform their expected tasks.
They should be equipped with relevant skills for operating IT devices (Stoneburner et al., 2002). This would result in the reduction of errors or losses of information. Another concern is the quality of IT supplies. Their durability and portability are crucial (Stoneburner et al., 2002).
This is for the reason that a durable resource works effectively, and a portable item can be moved to a new location in case of an emergency. Nonetheless, critical resources, such as local area networks server (LAN), wide area networks access (WAN), emails, and mainframe access, play important roles in designing a plan for IT components (Pollard & Hotho, 2006).
In addition, time is an important issue. The rate at which components of IT systems perform their tasks is determined by their initial programs, and would determine the time that would be spent (Pollard & Hotho, 2006).
Procedures involved in IT resource contingency planning
As aforementioned, it is important to plan for any disaster that would arise in any organization. There are certain factors that should be considered before any plan is developed. It is critical to indicate that this research paper would focus on desktop computers and portable systems, servers, websites, LANs, WANs, distributed systems, and mainframes (Pollard & Hotho, 2006).
It concentrates on ordinary technologies and would play significant roles in supporting contingency potentials (Pollard & Hotho, 2006). It is worth to note that when designing and maintaining an effective IT contingency plan, business managers should adopt the approach is discussed below.
Development of contingency planning statement policy obligations
This statement is indispensable in making stakeholders understand planning obligations. It is usually based on a well-stated policy and should state the overall objectives. Its roles and structure should be developed by all stakeholders (Nelson, Phillips & Steuart, 2010). The roles played by chief information officers are crucial in the success of the plan.
They should be engaged when developing the framework, aims, functions and roles of the plan. It is vital to point out that the contingency plan should be in line with guidelines outlined in NIST 800-34 (Nelson et al., 2010). Some of the features include the scope, preparation requirements, tasks and responsibilities, program of testing and exercise, how to maintain the plan, and how frequent backup would be.
Business Impact Analysis (BIA)
This is a critical step, and it enables the planning directors to categorize the system needs, development processes, and interrelationships (Nelson et al., 2010). The information obtained is used to identify priorities. This step is useful because it compares particular elements, studying the services that they provide using the obtained data.
Moreover, it helps to investigate the effects of interferences on other parts of the system. It engages other steps, such as outlining IT resources, recognizing the consequences of interrupted part, allowing outage period and prioritizing recovery approaches (Nelson et al., 2010).
Identification of preventive measures
This step aims at mitigating or eliminating impacts, which were identified in the second step (Lentzos & Rose, 2009). Arguably, personnel that would be involved in effecting control measures should be well trained in the methods of controlling and when to apply control measures (Lentzos & Rose, 2009).
In addition, the type of design of the system should be applied to determine preventive methods. One of the preventive measures is the application of an uninterrupted power supply. This would offer a short-term remedy to all system elements (Lentzos & Rose, 2009).
Alternative power sources, such as the use of gasoline, would provide long-term backups. Protecting IT equipment from water damage by using plastic tarps and utilizing technical security controls is another preventive measure (Lentzos & Rose, 2009).
Developing recuperation strategic approaches
According to Allen (2005), strategic approaches offer ways of restoring IT operations successfully in case there is service interruption. The methods are expected to focus on addressing the effects identified in the BIA. There should be a variety of strategies to be analyzed before the development of a strategic approach (Allen, 2005).
These factors include cost, time, and security (Allen, 2005). The chosen strategy should tackle possible effects that would be discovered in the BIA, which should be incorporated into the system during development and executing phases of the life cycle. Methods, such as the service level agreement (SLAs), reductant arrays of independent disks (RAID), UPS, and mirrored systems, among other strategies (Lentzos & Rose, 2009).
Creating a contingency plan
This is the most crucial stage in the process of executing an all-inclusive contingency plan program. It contains duties, responsibilities, teams, and steps in relation to IT system restoration (Allen, 2005). It should outline technical potentials, which would be supportive in the implementation of contingency operations. It should be modified to achieve a firm’s objectives and needs.
It is supposed to be balanced and flexible, and be in line with NIST SP 800-34 (Allen, 2005). It is imperative to point out that the IT resource plan in this research consists of five elements, which are supporting information, notification, recovery, reconstitution, and plan appendices (Allen, 2005). The initiative of the effective operations offers a framework of information, which simplifies the plan, leading to easier ways of understanding, executing, and sustaining the plan (Allen, 2005).
Allen (2005) contends that most details that are found in this section help to understand how guidelines and decisions about the plan are adopted. The notification stage is involved in describing the original actions, especially when a system interruption has been detected. Notification of recovery personnel, assessment of system breakdowns, and implementation of the plan are the main activities that take place at this stage (Allen, 2005).
At the recovery stage, the focus should be on the measures to implement provisional IT processes, renovating damages of the system, and restoring operational potentials of the original system (Allen, 2005). This will enable it to perform its intended functions. Many activities take place at this level, such as provisional manual processing, recuperation, and operation on an alternate system.
The activities help IT system to function as it is expected (Allen, 2005). A computer system starts to function normally at the reconstitution stage. However, if it becomes hard to recover the system, most actions at this level would target preparing new facilities that would be important in supporting the system (Allen, 2005). This should be done until the system is tested to find out if it has reverted to normal.
Appendices have particular technical, operational, and administrative contingency requirements of the system (Allen, 2005). Personnel contact information and vendor contact information are indicated in the appendices.
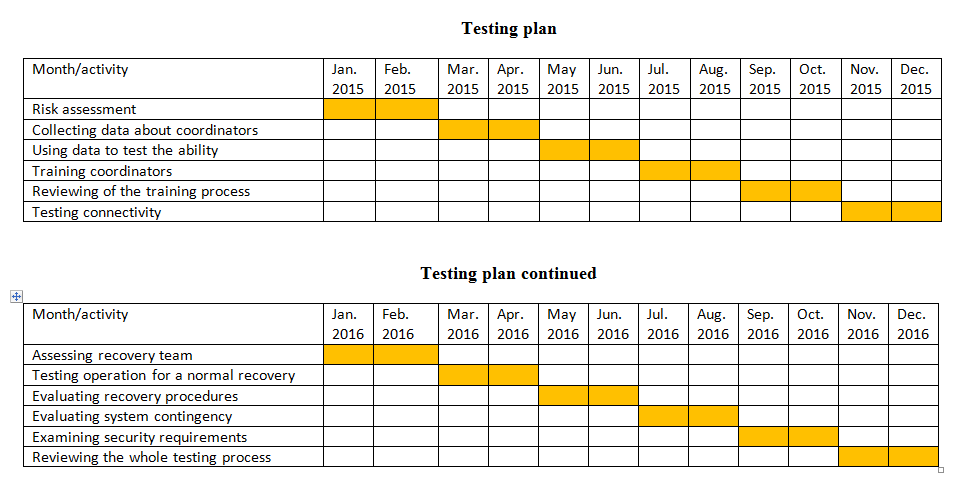
Plan testing, training, and trying it out
This vital feature aims at achieving workable contingency competencies. Testing facilitates identification of plan deficiencies and addressing (Swanson, 2011). Nonetheless, it is helpful in evaluating the ability of improving staff for the plan to be executed effectively.
Most of the tested areas are coordination among recovery teams, connectivity, and restoration of normal operations, notification methods, and system recovery strategies (Swanson, 2011). Personnel should be trained in relation to their roles. For example, the purpose of teams, the importance of team coordination, methods of reporting, security requirements, and team specifics should be highlighted clearly.
Plan maintenance
It is worth to note that for a plan to be effective, it must be maintained in a state that reveals its requirements, methods, frameworks, and policies (Nelson et al., 2010). This is due to the fact that IT is dynamic due to transfer of business needs, technology upgrades, and rules in companies.
Hence, it is important to review and upgrade computer systems on a regular basis. This should be done as “part of a firm’s change management process, and it is aimed at ensuring that new data are documented and control measures are adjusted” (Nelson et al., 2010, p. 76 ).
There are specific elements that require frequent reviews, such as lists of contacts and personnel. The management should inform all staff about the plan and their roles in implementing it. Revised plans should be distributed, but their copies should be maintained off-sites (Nelson et al., 2010).
Recommendations
Due to losses incurred during disruption of IT systems, it is important to develop control measures that would mitigate risks that would be involved. In the context of vulnerabilities of computer systems, service providers are required to review their contingency preparedness.
First, the management of a company should integrate IT recovery capabilities. As a result, this would recover the data that could be lost if the system would be interrupted. Market participants in the IT sector should make sure that IT continuity preparations are incorporated with continuity arrangements.
They should ensure that continuity arrangements are adopted to ensure effective IT systems during crises. It is important for IT management teams to retain emergency contact information for their primary corresponding companies.
The information contained in files should indicate preparedness strategies, site telephone numbers, and the main administrators’ contacts. It is advisable that IT personnel should occasionally review contact information that is availed to the management. During IT interruptions, staff should concentrate on applying the rules outlined by various groups.
Agency management teams should create their contingency policy and planning processes and utilize the features of the preparation cycle. These include preliminary planning, IT impact analysis, an alternative site selection, and recovery strategic approaches.
Moreover, the IT management team should conduct risk analysis. This would be vital in understanding the possible causes of interruptions and their effects. Surveys on the availability of alternative sites for the purpose preparedness should be conducted.
The focus should on the development of the right goals in relation to emergency preparedness. This would facilitate responses to IT problems. The planning process should be aimed at bringing changes in the IT industry. In addition, all stakeholders should be encouraged to understand the roles played by preparedness and contingency plans and tools applied in the process.
Attention should be given to the utilization of the process of contingency, enhancing the quality of the plan. All stakeholders should be accountable and responsible for managing funds that are essential in maintaining the contingency planning process. Planning and emergency responses should be linked.
Contingency plans should be adopted, but without preparedness actions, they become less useful. Prioritization of IT resources should be considered. As a result, improved mechanisms should be adopted to support effective planning and preparedness. Collaboration between the government and private sector would play key roles in implementing contingency planning and preparation.
Conclusion
In conclusion, IT systems are vulnerable to disruptions, which range from minor to complex interruptions from different sources. However, some of the interruptions can be mitigated, but not eliminated. This is possible through risk assessment and operational solutions.
The short-term measures adopted in this paper include changing the location of IT systems to preferred sites. Various steps are involved in the planning process. Each step is characterized by different activities that enhance the effectiveness in the management.
The IT resource contingency planning focuses on improving performance outcomes since IT is a basic tool in the management of companies. Firms have increased their output and reduced costs through the application of computer systems. Therefore, key issues should be evaluated before developing the IT resource contingency plan.
Risk assessment, staff available, software, and hardware are among factors that should be considered. These factors play vital roles in mitigating issues in relation to disruption that could arise in organizations. Despite the challenges of interruptions, companies are encouraged to continue using IT systems in order to thrive in a competitive business world.
References
Allen, W. H. (2005). Computer forensics. IEEE security & privacy, 3(4), 59-62.
Cerullo, V., & Cerullo, M. J. (2004). Business continuity planning: a comprehensive approach. Information Systems Management, 21(3), 70-78.
Lentzos, F., & Rose, N. (2009). Governing insecurity: contingency planning, protection, resilience. Economy and Society, 38(2), 230-254.
Nelson, B., Phillips, A., & Steuart, C. (2010). Guide to computer forensics and investigations. Cambridge, MA: Cengage Learning.
Pollard, D., & Hotho, S. (2006). Crises, scenarios and the strategic management process. Management Decision, 44(6), 721-736.
Stoneburner, G., Goguen, A., & Feringa, A. (2002). Risk management guide for information technology systems. Nist special publication, 800(30), 800-30.
Swanson, M. (2011). Contingency Planning Guide for Federal Information Systems. New York, NY: DIANE Publishing.