Brief Summary of the Project
The project covered in this report involves implementing and integrating a centralized transportation system for ten hospitals, utilizing cloud technology, which is a current trend in healthcare provision. The primary objective of this project is to implement a reliable technological upgrade that will enhance clinical practice. Examples of electronic applications that facilitate the transition include TeleTracking XT and BedWatch, which ensure convenient tracking and digital mobilization of patient logistics within a medical environment. The other key objective is a centralized system for configuring patients and implementing them from a virtual point in the hospitals targeted.
The project is expected to be completed in approximately 12 months, divided into distinct phases with specific durations. Several key milestones and deliverables must be met for the project to succeed. For instance, the installation of digital equipment, linking accounts, and fruitful operationalization are essential milestones that will be covered. As shown in Table 1 below, the total cost is approximately $825,000.00, with various stages contributing to the cost implications. The project manager is expected to ensure customer satisfaction, complete the work scope, and control the project’s progress, as well as play a critical role (Chapter 10: The Project Manager, slide 7). Thus, the project meets the standard aspects of project management responsibilities.
Table 1 – Project Costs
Discussion of Project Risks
In all projects undertaken, underlying risks contribute to the drawbacks experienced before, during, and after the implementation of various deliverables. Awareness of potential risks is essential, as it enables the analysis of feasible mitigation strategies that can be applied throughout the project (Gachie 325). As a project manager, one is tasked with critically analyzing anticipated risks and determining the necessary actions to prevent falling prey to them. Additionally, any potential risks need to be institutionalized, which is key for stakeholders, as shown in Table 2 below. Initiating change can help mitigate any perceived risk.
Table 2 – Applying Change Management Concepts to Combat Risks. Source: Chapter 10: The Project Manager, slide 27.
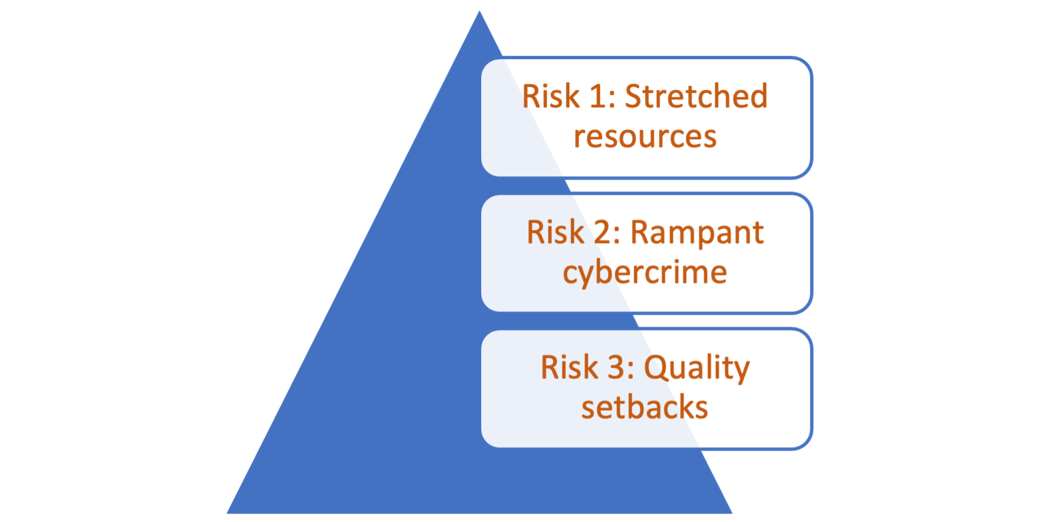
It is essential to consider that failure to check and address risks in this project will result in fatalities and adverse exacerbations, contributing to poor health outcomes for patients (Gachie 315). This report addresses three key risks: stretched resources, rampant cybercrime, and quality setbacks, as illustrated in Figure 1. The risks require project leadership abilities, which necessitate a collaborative team approach, empowering the project team, setting high expectations, and demonstrating the ability to deliver the work (Chapter 10: The Project Manager, slide 13). Thus, the risks will be mitigated with an experienced project manager who knows how to execute roles effectively within the overall plan.
Stretched Resources
A lack of sufficient resources to complete a project may be a key risk if the team working on it underestimates the required resources or irrationally allocates them without factoring in avenues of consumption within the project. This project’s resources may include time, skills, financial resources, tools, and others. For instance, if there is not enough money to pay service providers, they will be pressured to deliver the work superficially, which poses another risk to the half-baked system and potentially leads to medical errors.
In this case, an application may be programmed incorrectly, leading to erroneous clinical prescriptions that could result in medical liability. Payment for outsourced services is essential because it enables the full implementation of robust, cloud-based programs that comply with the Health Insurance Portability and Accountability Act (HIPAA) (Duffy 158). Stretched resources lead to deviations from healthcare standards designed to protect individuals hospitalized or in critical care.
Skill is an additional resource that may mitigate potential risks. For example, health analytics are required to provide insights into information security, interoperability, data analysis, and software development in healthcare. Thus, if the individuals chosen for this project do not have the required expertise and knowledge, data-driven solutions for patients may be incorrect, leading to professional liability.
In a centralized hospital transportation model, all workers are expected to be productive, meaning they remain engaged in their work at all times (Duffy 126). For instance, a transporter who is unable to read and interpret system-configured data may not respond effectively to emergency issues. Thus, the project may fail if training is not fully provided to members expected to serve in clinical practice areas. Other drawbacks include a lack of required tools to maintain project metrics.
Rampant Cyber Crime
The world has witnessed the advancement of digital tools to support services, significantly impacting the healthcare industry. This project addresses the artificial intelligence (AI) tools necessary to support the transition from monolithic to microservice architecture in hospital settings. During the project, stakeholders must ensure that the element comprising data entry or patient records is relatively secure to prevent malicious access and tampering with the system for monetary and other gains. The ten hospitals whose operations will shift to centralized green transportation systems must work carefully to address information security concerns (Duffy 187). Thus, during the project, sensitive data must be scrutinized and configured to a high level of authenticity for the logging of applications that aid centralization.
Quality Setbacks
When undertaking a project, various products and services are typically expected to be offered to facilitate the completion of key milestones and deliverables. Several equipment and digital tools will be used in the project. The team in charge of procurement may knowingly or unknowingly purchase low-quality products, which affects the quality of the transition (Shirley, 188). For example, an outsourced firm may offer low-cost cables for data transmission to servers. The impact will be a frozen experience due to network traffic issues, leading to timeouts. This challenge threatens the hospitals’ operationality, as key functions, such as the intensive care unit (ICU), may be paralyzed, leading to fatalities.
Recommendations to Address the Risks
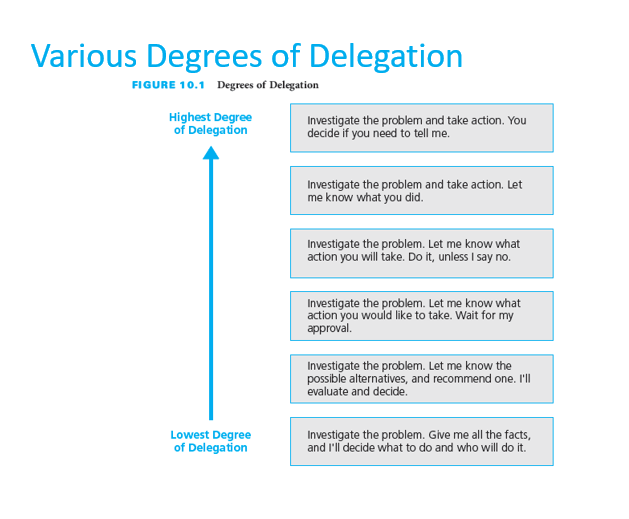
For the project to succeed, the underlying risks must be addressed promptly before they impact the project’s functional capacity. It is essential to recognize that any problem is a risk, which necessitates negotiating roles to address the problem and prevent the risk, as shown in Figure 2. All project resources must be planned in sufficient detail to avoid any deficit. That means funds, time, and other resources must be leveraged carefully, using a consultant who can forecast them and provide rational actions to safeguard the project from sabotage caused by resource setbacks. For example, the project manager must have sufficient funds reserved from bank loans, allowing any potential deficit to be covered by the financial institution (Shirley, 190). The time required to complete various milestones must be carefully checked to avoid work-related pressure at the end of the project.
Cybercrime issues in the project can be addressed to ensure a seamless transition. This can be achieved by implementing advanced security controls, such as integrating Zapier automation tools that prevent any threats and attacks (Shirley, 192). Additionally, implementing data encryption and off-site data backup are effective ways to mitigate the risk of falling prey to cybercrime issues during the project.
Regarding quality, the project management team needs to vet all avenues for service provision, product delivery, and any other alignment to support digital centralization. For example, a legally binding agreement should be in place between the project management and other stakeholders, such as suppliers and service providers, to ensure accountability in the event of any suspected failure. Additionally, to address the compromise in quality, the project management must involve people with expertise and knowledge in project auditing.
Integrating Earned Value Management in the Project
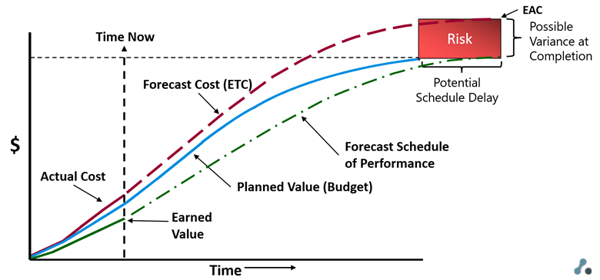
Earned Value Management (EVM) helps integrate cost, schedule, and scope of functionality, enabling the identification of problems and risks in project performance. This project will utilize various EVM metrics, including planned value, actual cost, earned value, and scope of impact (Breuker, para. 5). As shown in Figure 3, EVM can forecast costs and schedules, where risk can be assessed based on possible variance at completion. This tool will be helpful because it will ascertain the project’s consistency in transitioning clinical practice regarding patient transportation services.
Earned Value
In this project, earned value (EV) will serve as a key performance indicator (KPI) that provides a trajectory of the value of work completed within a given time frame. Specifically, the work breakdown structure (WBS) elements will be drawn and placed in a mathematical formula, considering the $825,000.00 budget that has been allocated. EV will also be used to check key stages of milestones such as operationalization and monitoring, among other WBS aspects, as covered in the previous report.
The specific methods to be used are discrete methods that cover the following: units completed, weighted milestone, and percent complete (Cummins para. 4). For example, launching an affected transport system under operationalization in the WBS for this project will be weighed based on planned resources. That means if the deliverable was planned to require resources worth $1,500.00 in the first quarter of the project, at the specified duration, the costs will be allocated to the project stage and checked to see if the total cost exceeds the initial plan.
If the transactions exceed the amount mentioned above, the value for the section of the WBS will not be earned. Instead, financial risks will be witnessed. If the figure tallies or is slightly under the projected one, the value is earned, and the project can be reported as safe. The same applies to the total cost for the project after one year, whereby the percent complete will be derived from the accomplished workload versus the full tasks (Cummins, para. 3). The percent will be calculated by taking the quantifiable ratio of work to give a projected estimate in terms of percentage.
Planned Value
The project is expected to deliver milestones and meet deliverables within a specified timeframe. To ensure this is within the safe zone, planned value (PV) will be applied to provide the baseline for project performance. In other words, the planned value for this project will be helpful if expressed as an overall figure(Mathew para. 2).
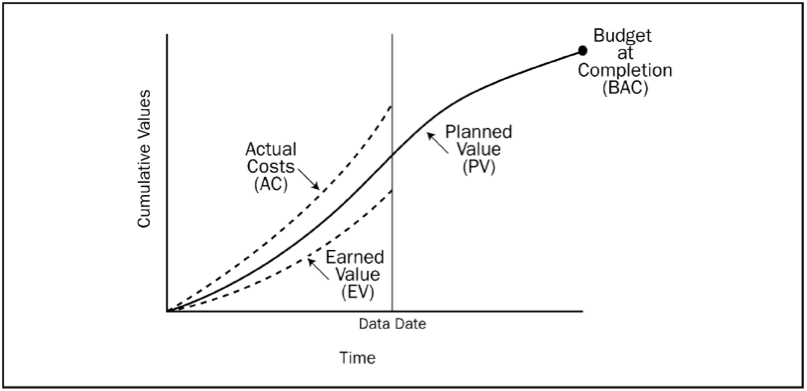
The PV will be used where the total cost shall be leveraged per time, where cumulative values will be seen after a date range, and comparison of actual costs, earned value, and budget at completion as seen in Figure 4 below. For example, if the percentage of the project completed is determined, the PV will be calculated by multiplying the percentage by the budget at completion. To ease these EVM metrics, the project focuses on achieving linear time and costs across all milestones.
Actual Cost
This metric represents the total cost incurred during the project. Actual cost (ACost) provides managers with a method to determine the efforts required to complete a project, thereby allocating expenditures or revenue to the expenditures incurred by and against an AR. This metric will be used in the project to determine the actual effort, and that will give a notation on whether or not the project was seamless in terms of costs (Cummins para. 4). This means direct costs, time, and other key aspects will be considered since there may be unforeseen multipliers in the project that might lead to margin variation.
Scope of Impact
This metric encompasses the project’s impact in terms of finances, knowledge, and the closure of existing gaps in the field where the project is relevant. It will be used to assess the scope of change regarding hospitalization, as it involves patient transportation in care facilities. At the end of the project, the project manager must determine the rate of transition and the outcome when it comes to healthcare mortalities (Mathew para. 4). For instance, the metric will be used to give a detailed report of how centralization of the transport system using AI and cloud leads to patient satisfaction and improved clinical services.
Works Cited
Breuker, Michael. “Earned Value Management: An Introduction.” Pinnacle, 2021.
“Chapter 10: Project Manager.” Lecture Notes, 2023, PowerPoint.
Cummins, Sean. “Planned Value in Project Management.” Jexo, 2022.
Duffy, Vincent G. Digital Human Modelling and Applications in Health, Safety, Ergonomics, and Risk Management. Human Body and Motion 10th International Conference, DHM 2019, Held as Part of the 21st HCI International Conference, HCII 2019, Orlando, FL, USA, July 26-31, 2019, Proceedings, Part I. Springer International Publishing, 2019.
Gachie, Wanjiru. “Project Sustainability Management: Risks, Problems and Perspective.” Problems and Perspectives in Management, vol. 17, no. 1, 2019, pp. 313–325.
Mathew, John. “Basic Earned Value Management Metrics for Design Consultancies.” BST Global, 2021.
Shirley, David. “Project Management – Pharma and Medical Device Manufacturing.” Project Management for Healthcare, vol. 3, no. 5, 2020, pp. 183–192.