In the business world, a signature is one of the most vital requirements when it comes to sealing of agreements. For instance, when two parties get into a contract, both parties must sign the contract as an indication of their commitment to the terms and conditions of the contract. In the event that one of them breaches the contract, these signatures may serve as evidence, in a court of law, that the parties were in an agreement.
Every handwritten signature is unique in terms of velocity, inclination angle and timing. This signature can be analyzed forensically against a sample signature to prove the identity of the signatory. A signature can be forged but it can never be duplicated: no two people can sign identically (Wright, 2007).
Unfortunately, this is only possible with pen and paper technology. With advancement in information technology, paper work has become almost obsolete. Transactions are carried out electronically hastening the whole process. However, this new development comes with its challenges; one of these challenges is how to attach a signature that is legally binding. In this paper, the legal issues of digital signatures will be discussed.
A digital signature is a cryptographically designed code that is attached to an electronic file to verify the authenticity of the sender. Before embarking on the contracting process, the two communicating parties agree on a system of encryption that they will use. They need to protect the data files that they will be exchanging from third party interference. Each of them comes up with a pair of keys known as the public and private keys.
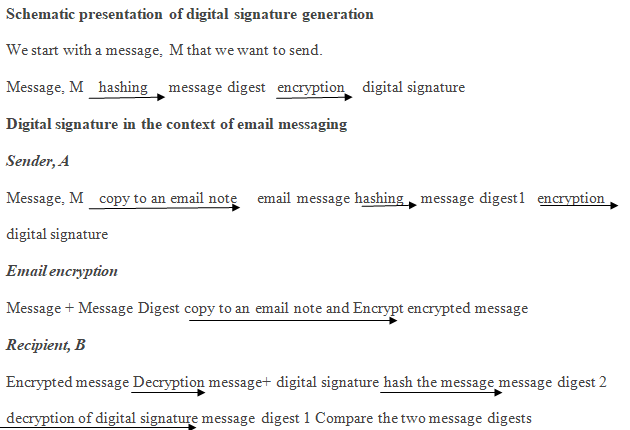
They exchange their respective public keys and keep their private keys secret. When party A wants to send a message to party B, party A runs the original message through a hashing algorithm to produce a message digest. The message digest is then encrypted using B’s public key.
The resulting code is known as the digital signature and is appended to the message which was initially encrypted with B’s public key. On receipt, B uses his private key to decrypt the message obtaining the original message and its message digest. The original message is run through a hashing algorithm and the result is compared with the digest received. If they match, then the integrity of the message is assured.
A digital signature, like a handwritten signature, should be unique for it to be valid. This means that a plainly typed name at the end of a document does not constitute a digital signature. A hacker may intercept the file in transit and formulate his own file, type the name of the genuine sender and send it to the intended recipient. The receiving party will not have a way to verify the source of the file.
On the other hand, a malicious party may intercept the file, make some alterations and resend it posing as the genuine sender. Again, the recipient cannot verify the sender. Such issues are some of the many security issues in the world of e-commerce. If a file that contains instructions to the receiver is altered maliciously, the execution of the resulting instructions will lead to huge losses.
On the other hand, without a legally binding signature, the contract law will be useless. It will be impossible to protect the parties that are getting into an agreement if there will be no prove that the two have actually agreed on such and such terms.
The major importance of a signature is its legal aspect. In business, a signature as seen under the contract law serves to signify commitment to the terms of an agreement. Secondly, it serves to eliminate repudiation (Mattord and Whitman, 2011). However, in e-commerce, a digital signature on its own does not serve as enough evidence.
It must be accompanied by business records as hearsay to substantiate the proof of the signature. The documentation must also be accompanied by a clear explanation from an IT professional involved in data processing and storage throughout the contract period. The person involved must prove what the signatory in question intended when he/she signed the document.
Another issue that arises to challenge the digital signature is the security of the particular contract. He must be able to prove that there is no possibility that the document may have been tampered with after it was signed. If the integrity of the document is questionable, that signature cannot be used as evidence (Mason, 2009; Mattord and Whitman, 2011).
To overcome these challenges and strengthen a digital signature as evidence, it is important to observe the security issues relating to the document. This is possible by applying cryptographic techniques in the generation of signature and in contract storage and transfer.
To achieve this: first, the contract should be transferred and stored in an encrypted format. Secondly, when generating the digital signature, the contract should be used to generate a message digest by hashing. The hash algorithm used can be used to generate the message digest once again in the event that evidence is required in court. If the original hash matches with the new one, then the document’s integrity is valid.
References
Mason S. (Editor). (2009). Digital Evidence and Electronic Signature Law Review – Volume 6 Pario Communications Limited.
Mattord H., & Whitman, M (2011). Readings & Cases in Information Security: Law & Ethics (1st ed.). Cengage Learning.
Wright, B. (2007). E-Signatures: Are We Building Sufficient Electronic Evidence? Web.