Abstract
Malware is software, which performs malicious actions on a network once it gets access to it. Malwares are destructive hence; they are unacceptable in any organization network. The desire of every organization is to have a network as safe as possible. In today’s networks, various threats are eminent and their modes of attacks keep changing every day.
This is a common challenge to networks; even the World Wide Web. In essence, the struggle of every network is to discover the most appropriate preventive, protective and corrective strategies against malware. Some networks apply malware-detecting systems.
They do this by implementing software known as sandbox to monitor the behavior of programs in order to ascertain whether they are malwares or not. Sandbox is a vital tool for decision making regarding relevant treatments to malware threats upon detection. This paper dwells on the execution of various methods to protect networks against possible malware attacks, inclusive of sandbox.
Introduction
The rate of Computer usage has increased tremendously especially owing to the use of internet and multimedia applications. Another contributing factor is the declining computer prices as well as internet connection costs, accelerated by the higher speeds of connection. Internet encourages disguise of identity among users. Studies have shown that approximately 80% of subscribers to social sites use anonymous identity to communicate, a fact that promotes internet crime (Couture & Massicotte, 2009).
Similarly, malwares originate from unknown sources yet their impacts are devastating. Malware suppliers masquerade as noble solution providers on the internet to unsuspecting users. A malware code exists as a single auto run file with the destructive instructions. Implementation of malware protection is necessary including disabling of auto run applications. A risk evaluation of every file is equally vital. This is where a sand box plays an essential role.
Examples of Malware
There are various types of malwares with various modes of attack on systems. Malware cause destruction to systems by deleting files, corrupting file contents, causing system failure and even stealing system access information. One type of malware is the Ransom ware Trojans.
This is an executable code, which captures and encrypts files on the attacked system. What follow a ransom ware attack is that the malware creators issue the decryption keys to victims but demand payment (Couture & Massicotte, 2009). The second type of malware is Password Reading Trojans. This type steals system access credentials such as login user names and passwords. They even steal passwords for emails, databases, games and secret financial information for banks.
The third malware is the Key loggers. This is a malware, which keeps track of the keystrokes, records every typing and sends to a remote computer. This malware also aids in password stealing. The challenge in dealing with key loggers is that some vendors sell them as genuine software for legitimate purposes. The attacker can perform a variety of actions including installation of other malware, fraudulent financial transactions and installing other malware codes.
Network Vulnerability
The Internet is currently highly insecure. The need for internet protection is in the area of virus protection, data encryption and decryption, access privilege control and the use of firewalls to safeguard data in the computer. The large number of internet users exposes various networks to external attacks and breach of civic obligation. Aside from that, computer users connected to the Internet also have a civic responsibility (Khouzani et al, 2008).
Failure to update antivirus protection or to enable an active firewall compromises the system and subjects it to attacks that are more serious. Another option, which is an alternative to virus protection, is to reduce the duration of internet connection. This implies that whenever internet is not in use, the user has to disconnect the internet. A Malware are ever ready programs on the internet, awaiting user actions so that they can auto run.
Majority of today’s security control measures to malware defense are more passive than they are active. They concentrate on reinforcing defense on attacks without first soliciting vital information about the possible attacks. The condition worsens with time owing to the aggressive nature of malware attackers as they aim at maximizing on their financial gain. Malware attackers have fundamental advantages over the network administrators, because they quickly realize the security lapses, much before the system administrators.
There is need for more intensive research, focusing on proactive malware defense mechanisms to identify existing potential but undiscovered vulnerabilities. This can be more effective if the defense mechanism detects and fixes the vulnerabilities before the malware attackers take advantages, and before they attack the entire system.
Present Security Situation
The rapid spread of information coupled with practical security challenges has enabled people to acquire Network security awareness. This has brought along new techniques to scrutinize network security situation. The rate of antimalware systems and data recovery applications is fast accelerating, indicating the index of security awareness (Khouzani et al, 2008).
Nevertheless, the vulnerability of networks to malware attacks remains high due to increased use of social networks. The multimedia data usage also jeopardizes the security situation. Most of the games and entertainment programs contain malware codes.
Malware coders target these considering that the probability of their usage is extremely high and proportional to the populations of youths. Approximately 69.8 % of social network subscribers have encountered malware attacks at least once in their process of socializing (Grain et al, 2001). Some of the malicious codes also spread through emails. Notwithstanding the availability of anti malware programs, the challenge is how to maintain regular updates.
Possible Attacks
Malwares exist in form of various programs codes such as worms, virus, Trojans and spyware. They move from one system to another through storage media and various communication channels. A virus attacks at least one file in a vulnerable computer system then it spreads to other files. When this file reaches other computers, it continues to infect the files in those computers as well. Worms are equally destructive as they destroy data on computers.
They can clog and slow down network systems by performing unauthorized electronic communications. Worms can generate additional copies of files on a computer, initiate and send emails to other computers containing the infected file. Unlike viruses, worms do not necessarily require human actions to move to other computers.
Trojan horses have the capacity to cause a computer or a network system to perform unanticipated actions, which are detrimental to the system itself as well as its user (Grain et al, 2001). This category of malware masks itself in emails. It can also hide in web sites, targeting unsuspecting users. Spyware is a system in the form of a website, which monitors the user’s actions while navigating a particular website.
Spywares are not entirely disastrous because they provide vital information about a Web site, which can help in improving the design of the website. Regrettably, some hackers use spyware to install malware on unsuspecting computers. A war dialing dials a series of successive phone numbers in attempt to locate a modem at random. Once it accesses a modem, it takes control over the network and performs malicious actions. The table below gives a sample data of malware attacks on social networks in 2011.
Table1: Malware Attacks on Social Networks in 2011
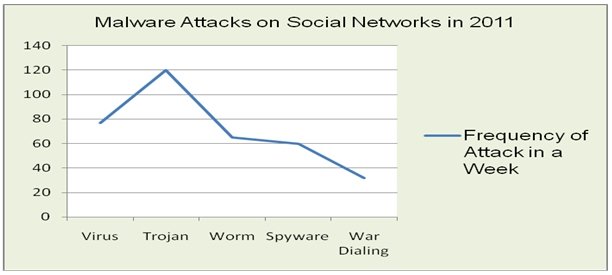
Figure 1: Malware Attacks on Social Networks in 2011
Sustainable Solutions
Malware attacks in the modern world of technology have grown dynamically in the use of variety of methods to perpetrate crime. Perhaps the optimal approach for antimalware defense is the use of more proactive solutions (Goranin et al, 2001). The ideal approach is to make computer systems, networks, databases and websites as less vulnerable as possible.
The system administrator stands a proactive chance to initiate the process of identifying the possible vulnerabilities of the system in order to eliminate them. Rather than make efforts to block 100% of possible attacks, it is safer to make the network immune to external attack (Patidar, 2011). Malware attackers use botnets; automated programs with the capability to identify vulnerability of a computer system. Botnets use only few parameters to assess vulnerability, and these parameters are limited to an automated knowledge base.
This means they cannot detect vulnerabilities, which do not match the descriptions in the knowledge base. To win the war against botnets, it is necessary to access and install missing patches, reconfiguring vulnerability parameters and restricting access to web server-based applications. System vulnerability status requires a periodic check because malware keep regenerating on a daily basis (Patidar, 2011). The second approaches include audits to server logs and firewall logs.
These logs have to undergo periodic updates to be able to eliminate system vulnerability to malware attacks. Closely related to this is the third strategy in fighting malware, which is the periodic monitoring of new installations. New installations are intruders to the system until they pass the vulnerability confirmation test. The forth strategy is Monitoring of system performance. Any unique and suspicious system behavioral change is an indicator to vulnerability status, and needs serious attention.
Figure 2: Firewall in a Network
Finally, antimalware demands periodic monitoring of anti-virus protection. Any system or network must have an antivirus, which again requires periodic update to be able to fight the newly generated virus, worms and Trojan horses. The validity of update definitions lasts for a standard period of between thirty to sixty days.
Cited Instances of Security Threats
In the recent past, viruses and other malware codes were nothing other than mere hoax to make life more interesting. However, today’s Internet security attacks relate to the intention to earn money. A research in 2005 from a University in Indiana revealed that seventy percent of phishing attacks on social websites actually succeed.
The victims to these attacks ended up exposing their secret codes such as usernames and passwords, bank account details and other private matters. In the first quarter of this year, Twitter encountered uncountable phishing attacks. Malicious criminals designed a web page, which resembled Twitter page and used it successfully to play hoax on unsuspecting users.
Social sites are the present targets of malware attacks, according to network security experts (Radmand, 2009). In 2004, Russia released a malware attack on USA military network and stole vital security information. Later on in 2008, USA retaliated by sending a malware which deactivated various private and public website in Russia (Valeriano & Maness, 2010).
Challenges to Antimalware protection
In spite of the tireless efforts of security experts to fight malware crimes, some malware writers create immunity against antimalware software. This causes a serious threat to vulnerability detection and prevention. The other challenge is that malware designers produce malware and viruses that are more complicated each day. Some programs are not easy to detect especially when the antimalware system has not been undergone update.
Malware programs often hide in the computer system in locations where no antimalware program can detect them. Finally, the challenge with malwares is that the rate at which the malware writers spread them on the internet (Radmand, 2009). They are more aggressive than the system users, since their principle aim is to earn monetary return. Consequently, the number of attacks at any one time on the internet becomes overwhelming to the system users.
Conclusion
Security is a very vital subject whose aspects everyone ought to understand. A user needs to know the levels of risk that are tolerable. For a successful fight against malware, systems need to comply with standard security policies. From a regular assessment of a system security situation, it is very crucial to find out the areas, which need improvement, to guarantee permanent security against malware. A great percentage of network administrators are ignorant of their security weaknesses.
They prefer easier options of using default security configurations instead of customizing security features. Unknown to them is the fact that malware attackers, with the use of botnets, easily detect these gaps, this being their fundamental objective.
System users often feel that security regulations are too restrictive and they formulate lenient options giving malware an upper hand. Security issue has always been solely the responsibility of system administrators. However, in the modern world, it has to be the responsibility for a successful fight against malware.
References
Couture, M & Massicotte, F. (2009). Using Anticipative Malware Analysis to Support Decision Making. Ottawa, Ontario, Canada: Communications Research Centre Canada.
Goranin, N., Cenys, A. & Juknius, J. (2001). Extension of the Genetic Algorithm Based Malware Strategy Evolution Forecasting Model for Botnet Strategy Evolution Modeling. Vilnius, Lithuania: Information Security Laboratory, Department of Information System, Faculty of Fundamental Sciences, Vilnius Gediminas Technical University.
Khouzani, M.H, Sarkar, S. & Altman, E.(2008). A Dynamic Game Solution to Malware Attack. Pennsylvania: University of Pennsylvania.
Patidar, P. (2011). Network Security. Indore: Swati Jain Academy.
Radmand, A. (2009). A ghost in software. Columbus, GA, USA: Columbus State University.
Valeriano, B. & Maness, R (2010). Persistent Enemies and Cyberwar: Rivalry Relations in an Age of Information Warfare. Chicago: University of Illinois at Chicago, Department of Political Science.