Executive Summary
The given study delves into the critical aspects of the modern aviations functioning and the work of the international organisations as IATA or ICAO aimed at the improvement of safety measures and creation of a secure environment needed to protect passengers, workers, and aircraft from the emerging threats. Mixed methods of research are used with the primary aim to investigate the issue and ensure efficient data collection.
An in-depth literature review is conducted to describe the current state of the civil aviation industry, new emerging threats and how these are touched upon by international organisations. A specific survey was designed to investigate employees perspective on the question and how they consider the efficiency of the suggested measures. Results of the literature review and investigation among workers prove that organisations recommendations remain efficient. Findings of the given project evidence the necessity of the further cooperation between aviation companies and agencies.
Introduction
The given research is designed following the pivotal aim to reveal the current state of the aviation security, fundamental problems and threats it faces today and how it manages to function regarding these issues. At the same time, diverse conventions and recommendations suggested by civil aviation organisations tend to improve the situation by setting new approaches to enhance the functioning of the industry are assessed and discussed.
The study explores the mixed qualitative-quantitative method to achieve the goal and provide information needed for the discussion of the issue and its fundamental aspects. The next section introduces the background information about the research, the aviation security, the current state of security, problems that arise and organisations responses to them. It provides a rationale for the research and justifies the selection of the given topic by offering a brief explanation why the research on this issue should be done.
Background of the Research
Today we can observe drastic changes in numerous spheres of human activity. The aviation industry is no exception. It is an extremely complex field characterised by highly sophisticated and complex processes fundamental to its efficient functioning (Abeyratne 2016). Thus the implementation of innovative methods and new technologies is expected to enhance these activities and ensure their error-free continuation. However, the creation of a new digitalised environment can result in the appearance of new vulnerabilities due to the nature of the software and technologies used in airports to organise their functioning and guarantee appropriate outcomes. For this reason, cyber security is becoming one of the major concerns of the modern aviation industry.
Moreover, modern society is characterised by a significant terrorist threat and new ways to organise terrorist acts (CANSO 2014). Such traditionally unstable regions as the Middle Eastern one, the war in Syria and numerous other conflicts introduce the need for improved security methods to avoid harm to travellers and guarantee safety to all passengers who use the aviation industry’s services (Ferguson & Nelson 2013; Esposito, Winderm & Winter 2014). In this way, enhanced anti-terrorist actions have today become the second main concern of the aviation sphere.
The human factor remains one of the leading causes of the emergent situations leading to various failures. The increased sophistication of modern technology along with the numerous duties and responsibilities that every airport worker has might result in the appearance of performance problems or a lack of understanding for basic tasks (Cromie et al. 2015). For this reason, the human factor often leads to undesirable outcomes and might create the basis for the appearance of loopholes in the security system. Mitigation of the negative impact of this element is one of the primary tasks of today’s aviation industry.
Many other factors appear every day that encourage the emergence of multiple problems in the aviation industry. These might include technological aspects, financial crises, political instability, etc. (Cromie et al. 2015). Moreover, the tendency towards an increase in demands on the quality of service creates a need for the constant improvement and alteration of outdated approaches with new ones which could also constitute a hypothetical threat, as their efficacy might be doubtful.
Thus international organisations like ICAO and IATA are monitoring the situation and the appearance of new threats that might result in the deterioration of the industry’s operations or more serious problems (ICAO n.d.a; IATA n.d.a). The organisations are responding to these menaces by creating specific recommendations and measures to eliminate loopholes and enhance the security system (ICAO 2016).
In this way, the given background results in the establishment of the central aim of this project which is the investigation of new threats that are appearing due to the rise of technologies and complex international relations, and measures that are being introduced by airports and international organisations like ICAO and IATA to minimise risks and provide passengers with security guarantees. Moreover, ways to reduce the negative impact of the human factor and mistakes in some activities are also investigated. The importance of the project lies in the continual appearance of new threats and the critical significance of the aviation sphere for the modern world.
Justification of the Research
The choice of the given research topic is preconditioned by several factors impacting the modern aviation industry and resulting in the emergence of alterations in it. First, the high speed of the development of society and technologies precondition the appearance of diverse issues that should be solved to guarantee the improved functioning of airline companies and safe transportation (Yool 2005). At the same time, methods that had been used in the sphere during past several decades demonstrate the low efficiency and are no longer able to protect passengers, aircraft, workers, and facilities from emerging threats (ICAO n.d.).
The tendency towards the further sophistication of the society, international relations, and technologies result in the diversification of potential problems that might appear in future and endanger the development of the aviation industry (Zan, dAmore & Di Camillo 2015). Moreover, Chicago Convention on international civil aviation remains the fundamental document regulating the functioning of the sphere; however, due to the factors mentioned above, its ability to suffice for airline companies and preserve the safe environment is doubted (Convention on International Civil Aviation n.d.).
For this reason, International Civil Aviation Organization (ICAO) and International Air Transport Organization (IATA) introduce specific amendments and conventions to ensure that the industry will be able to meet the existing threats and continue its evolution (IATA n.d.; ICAO n.d.c). However, the situation might still remain complex because of the complexity of problems that arise today and problems with the implementation of the suggested regulations.
In addition, aviation remains a strategic mean of transport that preconditions the high speed of globalisation and impacts the development of the international relations. That is why it becomes vulnerable to diverse terrorist organisations trying to destabilise the situation and undermine the basis of the society (Esposito, Winderm & Winter 2014). The rise of ISIS and Syrian war introduce new security concerns and increase the risk of terrorist attacks significantly (Whitehead 2014).
For this reason, its efficient functioning should be considered a key to the further evolution of the global intercourse and stable connection between states. Correctly realising the importance of the sphere, international organisations try to establish a safe environment that might decrease the number of emerging threats and provide companies with potent tools to face these challenges and overcome all difficulties (ICAO n.d.a). In such a way, regulations suggested by these agencies become one of the methods to adapt the modern aviation industry to the new conditions and ensure its efficient functioning regarding threats that appear due to the technological revolution and the complexity in the international relations.
Altogether, all these factors precondition the emergence of the need for the comprehensive investigation of the modern aviation security with the primary aim to determine the most problematic aspects that should be given attention and how the suggested regulatory measures contribute to the creation of a new safer environment and minimise risks associated with maleficent actions from third parties (Duchamp, Bayram & Korhan 2016). In this regard, the topic of our research is justified by the enhanced importance of the sphere, latest alterations in the approaches to security, and the need for the enhanced understanding of the nature of threats to respond to them.
Research Questions
Regarding the information provided in two previous sections and the existing need for the in-depth investigation, the following research questions could be formulated:
- Does the introduction of ICAO and IATA recommendations contribute to the creation of a new safer environment and minimise the level of existing threat?
- Has the existing approach to security altered under the impact of new factors including international organisations regulations and emerging threats?
- Do specialists working in the sphere notice positive alterations and accept the necessity of change?
- Can a new and safer environment regarding the civil aviation industry be observed today due to the implementation of new regulations, ICAO and IATAs contribution?
Moreover, the given research questions precondition the introduction of the following objectives:
- to analyse existing threats to the aviation industry and its security
- to discuss existing research literature and its perspectives on security systems
- to analyse the efficiency of strategies suggested by ICAO and IATA to eliminate:
- a terrorist threat
- a cyber security threat
- human factor aspects
- to answer how efficient are these strategies
- to discuss their advantages, disadvantages and limitations
- to assess specialists attitudes to them
- to create the basis for a future investigation
The given points will precondition the research and the choice of methods to achieve the established goals and guarantee the comprehensive investigation of the selected topic.
Literature Review
Introduction
The following section is devoted to the investigation of the relevant literature that delves into the selected topic. The given review will create the theoretical background for the research and provide data about the nature of emerging threats, their impact on the civil aviation industry, its responses, and regulations. Analysis of previous research works that delve into the given sphere will also help to trace alterations in perspectives on security in the field of aviation and methods that are used to ensure the preservation of the high level of protection to all individuals and facilities belonging to this very sphere.
In such a way, the given literature review offers the information about three basic aspects that might impact the functioning of airports and airlines. These are a terrorist threat, a cyber security threat, and a human factor (Dijbo 2012). All sources selected for the given section meet quality standards as they suggest relevant and credible information about the current state of the aviation sphere and its activity (Creswell 2014). We use databases, academic journals, ICAO and IATAs reports, online libraries, websites and other sources to collect data and create the theoretical background for the research.
The Basic Challenges of the Modern Aviation
Starting a discussion of the current state of the modern aviation security we reveal factors that might significantly impact its functioning and result in the emergence of diverse security concerns. The human factor is the first aspect that should be considered. It has been traditionally associated with the complex and responsible activities that demand the high level of knowledge, skills, and performance (Caldwell 2012).
For this reason, it is not a new problem the aviation faces today. However, as it has already been stated, the increased sophistication of the majority of activities that should be performed by an employee at his/her workplace and the pressure of responsibility that rises every year might result in the appearance of fatal mistakes and unpredicted consequences (Crevits, Labour & Vanderhaegen 2014). That is why specialists differentiate the human factor as one of the threats that should be considered to ensure the stable functioning of the aviation sphere.
Another threat topical regarding the modern international situation is the high risk of terrorist attacks. The given issue emerged in the previous century; however, the tendency towards the further aggravation of relations in the Middle-Eastern Region and in areas traditionally associated with the activity of terrorist organisations stipulate the further increase of the risk of attacks and maleficent actions (Security Case Study n.d.).
The problem is also complicated by the fact that old types of terrorism are replaced with new ones which include cyber attacks and other acts using innovative technologies and unusual approaches. In such a way, international organisations like ICAO and IATA show their disquietude about the functioning of the civil aviation regarding the potentially high probability of terrorist attacks (2016). The given factor is considered by specialists working in the sphere and agencies that try to establish a safer environment (IATA 2016). Specific regulatory actions, conventions, and security measures are suggested to minimise the risk of attacks and ensure that passengers, aircraft, facilities, and workers will be protected (Shay 2016).
The rise of another threat peculiar to the modern international civil aviation is associated with the rapid development of technologies and opportunities they provide to malefactors. The fact is that cyber security concerns acquire the top priority today due to the continuously increasing number of hacker attacks and significant damage done by them (Tamasi & Demichela 2011). Almost all spheres of human activity associated with the broad use of technologies and innovations become vulnerable to this kind of threat because of the appearing loopholes in security systems discovered and explored by hackers with diverse purposes.
Regarding the civil aviation sphere, its functioning might also be corrupted by using innovative technologies to interfere with the stable work of all security systems and create a potentially dangerous situation. In addition, cyber terrorism, as a new generation of terrorism, also poses a significant threat to security and safety of all passengers using civil aviations services (Arasly 2005). Specialists state that terrorists might also precondition the crash of airplanes by destroying specific onboard systems regulating the flight (Drury & Shipman 2010). For this reason, it should be taken as another threat that might corrupt the functioning of the system.
The Current State of Security Concerns
Having outlined the three basic problematic issues associated with the civil aviation sphere, it is also critical to outline the current state of the basic security concerns and extent to which these endanger the industry. In accordance with the recent research, we can observe the gradual decrease in the number of accidents (see Fig 1 in Appendix) that is achieved due to the improved security measures and combination of different approaches with the primary aim to deal with all kinds of threats (Statistic analysis of airplane accidents n.d.). At the same time, the number of onboard fatalities remains high which might indicate the presence of significant problems related to other security concerns like the human factor and cyber attacks (Dijbo 2012).
Moreover, analysing the primary causes for the appearance of accidents and diverse complications, one can see that there are different factors that impact the sphere and precondition the emergence of problematic situations (see Fig. 2 in Appendix). In its report related to the current state of the aviation sphere and challenges it faces, ICAO (2016) emphasises the fact that modern digitalised security gives rise to additional threats to aviation security.
For instance, vulnerabilities in specific software packages used by airports might encourage the emergence of significant problems with flight management or other aspects of the industry’s operation. In this way, the rise of new technologies facilitates the development of complex issues related to the sphere of aviation (ICAO 2016).
The given statement is justified by Duchamp, Bayram and Korhan (2016) who admit the tendency towards the increase in the number of software failures preconditioned both by human errors and maleficent actions of the third parties. That is why the modern aviation security experiences the stage of the constant increase in the risk of being attacked (Duchamp, Bayram & Korhan 2016). Moreover, these software failures and loopholes in security systems could potentially be used by terrorists to organise attacks and frighten passengers.
Thus Hall (2015) outlines the unique importance of creating a specific culture of airport security capable of meeting the constantly emerging threats. The fact is that the ability of the existing approaches to meet all requirements is doubted by both people who use civil aviations services and specialists working in it (ICAO 2016). For this reason, to remain effective and provide both passengers and workers with safety guarantees, any airport security system should possess a certain level of flexibility and adaptive capability (Hall 2015). Only under these conditions will airports be able to maintain high-level protection by evaluating the threats and problems that appear every day (Abeyratne 2016).
This pattern should become central for aviation, as it guarantees enhanced results and potent monitoring and security tools. Nevertheless, Raphael (2013) is also concerned about the current state of the security system in aviation and its ability to face existing challenges. Focusing on this issue, the author outlines the major challenges of the industry which also include terrorist attacks, cyber threats, human factors, software problems, and states that all countries that provide civil aviation services to individuals suffering from the same problems and challenges preconditioned by the increased sophistication of methods used by malefactors (Raphael 2013).
Speaking about the current state of the aviation industry we can also admit that in accordance with the relevant statistics a certain increase in vulnerability of specific areas is noticed (see Fig. 3 in Appendix). In such a way, regarding the tendency towards the further rise of risk factors, the current state of the aviation security can be described as the problematic one. In addition, data about most recent aviation accidents and the reasons for their emergence shows that the majority of modern states might demonstrate high vulnerability (Raphael 2013 This idea is supported by Price (2013) who outlines the current guidelines that are accepted in aviation security to minimise potential threats and ensure that no serious accidents will happen.
The author admits that we now are able to observe a shift of priorities towards the creation of new systems that will be characterised by enhanced flexibility to respond to new threats. It evidences the limited capacity of approaches that have traditionally be used in the aviation sphere. Price (2013) is certain that the use of innovative technologies will help to address the majority of new threats and guarantee that aviation will remain the safest means of transportation.
However, we now face the extremely complex task of adapting systems to new conditions and ensuring that all organisations are ready to act regarding the new requirements and demands for efficacy and safety (Cromie et al. 2015). Singer and Friedman (2014) are also certain that we can now observe the first stages of cyber war in the rapid development of technologies and their wide implementation in the sphere of aviation.
Moreover, in accordance with the research of the UK Centre for the Protection of National Infrastructure (2012) civil aviation faces a high risk of being attacked by hackers or cyberterrorists, and it increases rapidly because of the appearance of new communication techniques, technologies and the Internet which is now used as a central and potent tool for diverse interventions. In this way, it is becoming crucial to evaluate the nature of the threats now appearing and their potential. At the same time, specialists have also discovered numerous vulnerabilities in existing security systems emerging from the increased sophistication of the methods to attack them and perform injurious acts (Ferguson & Nelson 2013).
As it has already been stated, despite a certain decrease in terrorist activity observed in recent years, the risk of attacks remains high (Arasly 2005). For instance, research conducted by ICAO (2016) shows that commercial airlines might still be attacked by terrorists who have diverse purposes. It means that today the sphere of civil aviation experiences a great threat that comes from the rise of terrorism, increased power of ISIS, and anti-terrorist war in the Middle-Eastern region.
Altogether, the current state of the primary security concerns could be described as a complex one. All states using the aviation services and engaged in the international discourse might suffer from numerous attacks or other aspects deteriorating the functioning of the field.
Authors also admit that the existing security measures should be supported by new recommendations and conventions suggested by organisations as ICAO or IATA to ensure that the high level of security will be preserved. Revolving around the three basic threats that endanger the industry today, Rankin (2010) state that the ability to struggle regarding the cyber war, terrorist attacks, and complexity of tasks suggested to workers should be cultivated by the introduction of a new environment with innovative approaches.
The Human Factor
The modern science identifies human factor as a unique phenomenon that encompasses numerous social, biological, physiological, and other features of individuals or their groups that determine the efficiency of multiple processes and their outcomes (Hancock & Hart 2002). In the paper, it has already been mentioned that diverse organisations still consider it one of the most important threats to the field of civil aviation, security, and flights. Statistics show that from 15 to 30 % of errors in diverse spheres occur under the impact of this very aspect (Ferguson & Nelson 2013). It is apparent that the given range is too high for the industry that works with people and remains responsible for their lives (see Fig. 4 in Appendix).
At the same time, numerous catastrophes and accidents prove the fundamental character of this issue (ICAO 2016). ICAO and IATA are also aware of the problematic nature of this aspect and outline a significant need for the alteration of the existing approach to the human factor in the sphere of aviation security (ICAO: Human Factors documents n.d.). In accordance with ICAOs reports, the disregard of this critical aspect might result in the gradually growing risk of failures in flight operations, pilots critical mistakes, their inability to make an appropriate choice, deterioration of security systems, decrease attention, and poor specialists performance (Krause 2003).
This concern is proven by the fact that the bigger part of the accidents is associated with misbehaviour of the flight crew or their wrong decisions (see Figure 2 in Appendix). Under these conditions, ICAO (2016) recommends all states to accept measures aimed at reducing a pernicious impact of the human factor on the functioning of diverse security systems. Moreover, the organisation is sure that there is a dependence between the workers preparedness and the way airports function and organise security measures (Price 2013). That is why the human factor should be considered a key element in modern civil aviation.
However, the risk of failure under the impact of the human factor and undesired mistakes increases every year because of the high sophistication of duties workers should perform to organise stable and efficient functioning of an airport and the wide use of technologies that might be difficult for individuals. Demosthenous (2007) states that the majority of errors related to this aspect occur when human factors, the environment, and technologies interact (see Fig. 5 in Appendix).
It means that the introduction of the effective system that will be able to face all challenges and provide security guarantees to passengers and workers is possible only if all workers correctly realise their duties and have no difficulties with the use of innovative technologies suggested by diverse organisations as preventive measures (Schwaninger 2006). ICAO states that “the safety output is best illustrated by past accidents where Human Factors have been either the cause of the accident or a contributory element to it” (ICAO: fundamental human factors concepts n.d., para 3).
At the same time, the organisation suggests the most frequent reasons for the appearance of errors of this sort which include poor crew resource management, over-reliance on automation, violation of standards and regulations suggested by international agencies, misinformation, miscommunication, lack of assertiveness, visual illusions, etc. (ICAO: fundamental human factors concepts n.d.). In such a way, accepting the unique importance of the given factor and its role in the evolution of the existing approach to security, ICAO and IATA also admit its problematic state and need for the continuous improvement (ICAO: Human factors documents n.d., IATA 2017).
There are several basic reasons for it. First, reducing the probability of error caused by the human factor, international organisations might contribute to the significant improvement of the functioning of the civil aviation sphere by minimising the number of crew errors and eliminating risk (Yeh et al. 2012).
Second, the elimination of the pernicious impact of the human factor is closely related to the additional training provided to workers with the primary aim to enhance their competencies and ensure stable functioning. For this reason, ICAO and IATA outline the necessity of specific attention for this aspect as it will help to create a new environment characterised by the reduced risks of hacker attacks of cyber terrorism because of the improved employees skills (ICAO: fundamental human factors concepts n.d.).
In this regard, some regulatory measures suggested by these agencies are aimed at the improvement of the efficiency output by affecting “levels of motivation, flight deck design, crew training, supervision, adherence to standard operating procedures, crew resource management, etc.” (ICAO: fundamental human factors concepts n.d., para. 6). As it becomes evident from ICAO recommendations, motivation and commitment become central aspects that might significantly decrease the probability of error and reduce the risk of the emergence of problematic concerns (Sweet 2008).
It also means that today civil aviation cannot be imagined without numerous efforts aimed at the improvement of motivation and its efficient monitoring. This idea can be supported by diverse researchers statements about a critical role this factor plays in the performance, efficiency levels, and outcomes (Raphael 2013). Science considers motivation as a force that promotes a particular impact on a person and preconditions his/her activity and behaviour (CASA 2012). That is why it becomes apparent that this aspect is a central element of workers performance and commitment as a highly-motivated employee will demonstrate much better outcomes if to compare with other individuals who have no desire to work (Raphael 2013).
In addition to that, in the course of specific research, investigators concluded that inspiration and concentration levels also depends on motivation impacting their increase and reduction (Raphael 2013). Another fact is that a percentage of errors is significantly lower in employees who have a desire to work (Raphael 2013). For this reason, correctly realising these ideas and the role motivation plays, civil aviation should devote significant attention to the cultivation of motivation and its gradual rise among the staff with the primary aim to reduce the probability of error due to the human factor.
In such a way, human factor that is considered one of the threats to the modern aviation security becomes closely connected with motivation and performance levels as the key elements impacting the functioning of the whole security system, its basic elements, and outcomes. That is why today we might observe implementation of diverse methods to eliminate a pernicious impact of this factor and improve the situation. One of the approaches includes the use of innovation and digital devices to reach higher efficiency levels and attain success (ICAO 2011). ICAO (2011) suggests combined approach that presupposes the integration of newest technologies that monitor workers performance and strategies aimed at the improvement of expertise, basic knowledge about human factors impact, and motivation levels.
Cyber security
As it has already been mentioned, the rise of digital technologies preconditions the emergence of a cyber threat to the functioning of the modern civil aviation. Due to this fact, organisations such as the International Coordinating Council of Aerospace Industry Associations (ICCAIA), the International Civil Aviation Organisation (ICAO), Airports Council International (ACI), and the Civil Air Navigation Services Organisation (CANSO) decided to engage in cooperation with the pivotal aim to coordinate their actions regarding cyber threats and eliminate all vulnerabilities that might threaten civil aviation, passengers, cargoes, and the staff (CANSO2014). This decision is central to the industry as it helps to evolve and resist emerging problems in terms of the cyberwar that could be admitted today due to the gradual increase of hacker attacks annually.
The problem is complicated by the fact that the constant emergence of new ways to interfere with the functioning of airport security systems and cause serious damage to their functioning (Center for International Law 2012). Radical reconsideration and reorganisation of workplaces under the impact of digital devices also facilitated the emergence of threats to security systems and loopholes that could be used by individuals (see Figure 6 in Appendix).
Specialists also admit the fact that today airports, their departments, and aviation organisations share crucial information using specific networks and devices which increases the efficiency of their functioning and, at the same time, provides malefactors with new opportunities to organise cyber attacks (Ferguson & Nelson 2013). It also means that the demand for enhanced systems and improved approaches to data sharing will continue to deteriorate the situation in the sphere because of the emergence of vulnerabilities associated with the massive use of these very devices and tools (Ferguson & Nelson 2013).
That is why today cybersecurity is one of the leading concerns as it helps to protect aircraft and other facilities by eliminating vulnerabilities closely related to the extensive implementation of innovations and their further use for diverse purposes. The given term is used to describe multiple tools, guidelines, methods, technologies, and practices that are cultivated, promoted and utilised by companies and organisations with the primary aim to protect their networks and systems from attacks and create the basis for their stable functioning (Hall 2015). All these elements also evolve and get new aspects needed to create an improved environment.
Nevertheless, the rise of the given threat also preconditions the increased level of attention devoted to the creation of a joint approach to the security (Chitty 2013). The fact is that the threat of cyber attacks impacts diverse companies and countries because of significant divergences in their approach to the organisation of online security and creation of a safe environment (Dhavala 2014). In such a manner, the creation of the consistent and efficient approach to discover and manage the majority of the modern threats becomes critical for security specialists and their ability to function effectively.
One should also understand the fact that the rise of media and its ability to highlight all meaningful events and accidents introduces new demands to the efficiency of security systems as the image of civil aviation might suffer (Elias 2009). For this reason, the elaboration of the joint approach becomes the pivotal aim of the international organisations regulating the functioning of the sphere of civil aviation (Enerstvedt 2017).
ICAO (2017) also states that the work of all services of an airport might be affected by a significant number of threats and unexpected factors. Moreover, regarding the sophistication of problematic concerns, there are several classifications of cybersecurity problems and concerns. One of these suggests considering the type of threat and its character while CANSO, as another organisation that is focused on the analysis of cybersecurity concerns and ways to eliminate these problems, offers the approach focused on the investigation of the basic motifs for performing maleficent actions as it is one of the fundamental aspects of a risks assessment and cyberwar civil aviation faces today (CANSO 2014).
In accordance with the given approach, the degree to which a particular attack is prepared determines its hazardousness (see Figure 7 in the Appendix) and indicates the need for certain actions to protect employees, passengers, and facilities. Unfortunately, the scale of the problem is significant and continues to grow because of the diversification of software and technologies (Rankin 2010). Hackers or cyberterrorists can utilise a wide variety of tools, resources, and approaches to cause harm to security systems. Due to this fact, a single airline company, organisation, or agency cannot find an efficient solution to the problem (Raphael 2013).
To overcome all difficulties and remain potent, all actors should cooperate with the central aim to create a safer environment and increase the level of information system security. This cooperation also preconditions the use of similar approaches to identify and classify potential threats with the primary aim to provide timely and efficient responses to them.
Under these conditions, appropriate risk assessment techniques become central to the industry as they might help to reveal all problematic situations and provide effective responses to them. In such a way, organisations like ICAO and IATA offer their recommendations regarding risk assessment approaches and their use regarding the situation. In accordance with IATAs (n.d.) investigation, the majority of approaches that are utilised by airlines to create a new and safe environment should be classified as three-pillar ones as they are focused on the enhanced understanding of all hazards, their assessment, and definition (see Figure 8 in Appendix).
The effectiveness of these strategies remains high especially regarding the increased complexity in the functioning of modern airports and challenges they face. That is why risk assessment is taken as one of the most important practices needed to investigate existing problems and ensure introduction of powerful security measures. Organisations such as ICCAIA, CANSO, IATA, and ICAO are also sure that risk assessment procedures are central to the shift of priorities towards a new improved framework because it will help to trace and respond to all problematic concerns and hazards in advance, reducing an opportunity of terrorist attacks or maleficent actions (CANSO 2014).
These organisations also offer a specific classification of threats: intentional, unintentional, targeted, non-targeted (CANSO 2014). IATA and ICAO (2016) also define risks by their sources which means that there are the following groups: foreign nations engaged in economic and information warfare; virus writers, former employees, terrorists, etc. (ICAO 2016). The existence of these classifications is central to aviation as they help to evaluate risks that might precondition failures or collapses in airline security systems (Krause 2003). In such a way, all organisations gradually implement robust measures and approaches to determine hacking threats and eliminate them (Price 2013).
The complexity of the problem of cyber security in the aviation sphere is also preconditioned by the fact that the number of operations performed by specific software increases every year (Zan, dAmore & Di Camillo 2015). Today, a common flight is supported by multiple operations and calculations made by the ground service (see Figure 9 in the Appendix).
Specialists state that the use of ICT has increased exponentially which also means the same rise in the number of threats that might deteriorate the functioning of the sphere and result in the emergence of unexpected situations or even crashes. At the same time, there is an obvious need to continue the implementation of these technologies as they help to minimise the probability of error due to the human factor. It proves the significance of the problem and the rise of numerous concerns related to the cyber security and cyber war.
Another emerging concern regarding the given issue is the tendency towards the further rise in the activity of such international terrorist organisations as ISIS (Special Meeting on terrorist threats to international civil aviation 2017). ICAO (2016) reports that it starts to use the practice of “hacking” to acquire the unauthorised access to computer systems and services with the primary aim to corrupt their stable functioning and create the basis for the emergence of new threats. There are Islamic State Hacking Division (ISHD) and Cyber Caliphate hacker organisations that work in the given sphere and conduct computer operations on behalf of ISIS or other terrorist organisations (Lawrence 2017).
In such a way, today we can observe the rise of diverse cyber threats and the tendency towards the sophistication of the situation in the sphere. The fact is that extensive use of technologies is a two-edged weapon as it helps to improve the functioning of the sphere from one hand and results in the appearance of numerous loopholes in security systems from another. That is why companies like ICAO and IATA are concerned about the creation of an appropriate approach to ensure the stable functioning of the sphere of civil aviation.
Terrorist Attacks
As we have already mentioned, terrorist attacks remain one of the central concerns of the modern civil aviation. According to ICAO (n.d.c), the risk of terrorist attacks remains high, especially in states involved in anti-terrorist actions in the Middle Eastern regions or in countries that were traditionally associated with terrorist activity. Under these conditions, Choi & Jae (2013) state that the global nature of the aviation and the wide participation of diverse states result in the emergence of new problematic issues that could be associated with terrorism and its spread across the world (Moores 2017). In other words, the further globalisation of our society results in the appearance of new opportunities for a strike.
Thus, Arasly (2005) is sure that the terrorist attacks of 11 September served as the turning point in the history of humanity marking the beginning of a new era characterised by the lack of stability, predictability, and other problematic issues (Price & Forrest 2016). At the same time, it remains the most crucial and devastating catastrophe associated with the civil aviation and the terrorist threat. It proves the enhanced efficiency of new security measures that now are implemented with the primary aim to avoid similar cases and create a new safer environment (Chair 2017). However, the recent event in the Middle-Eastern region and the further aggravation in the relations between states and extremist or terrorist organisations like ISIS make the issue extremely topical.
Chair (2017) states that today we can observe a new-wave terrorism characterised by the integrated use of diverse tools to conduct malicious actions and damage either an aircraft or facilities. The present-day terrorist is also considered a type of way that incorporates military, economic, financial, and cultural aspects with the primary aim to engage in a global conflict and scare individuals (Schwaninger 2006).
At the same time, terrorists avoid direct confrontation because of their inability to struggle with regular military forces or police (CTED 2017). It means that the shift of priorities towards the hybrid method of war is observed (Security guidelines for general aviation airports n.d.). Terrorists might explore different types of vulnerabilities, including cyber threat and human factors to acquire new opportunities for their attacks.
Moreover, in accordance with Counter-Terrorism Committee Executive Directorates (CTED) (2017) report, diverse terrorist groups organise their attacks against international civil aviation as a method to struggle against nations and cause as much harm as it is possible. Moreover, despite numerous actions taken to minimise the probability of these attacks, the society still experiences the risk of facing the international terrorism. For instance, on October 31, 2017, a Russian plane crushed (Azani, Lvovsky & Haberfeld 2016). It was flying from the Sinai Peninsula to Saint Petersburg (Azani, Lvovsky & Haberfeld 2016).
The explosive bomb was placed under a seat, and its activation resulted in the death of 224 people on board (Azani, Lvovsky & Haberfeld 2016). ISIS accepted its responsibility for the terror attack which became possible due to a serious breach in the airports security system. Unfortunately, this tragic terrorist act became the first in a chain of attacks performed by ISIS with the primary aim to undermine the functioning of the civil aviation industry and scare passengers across the globe (Azani, Lvovsky & Haberfeld 2016). On February 3, 2017, a passenger plane in Somalia was attacked using an explosive bomb (Azani, Lvovsky & Haberfeld 2016).
Another terrorist act happened in Brussels, Belgium on March 22, 2016. There were three powerful explosions. Two of bombs exploded in the airport area while the last one at the nearest metro station. Soon after the attack, a special board created to understand all peculiarities of the accident determined that two suicide bombers from ISIS were responsible for the terrorist act (Security Case Study n.d.). They analysed all features of the area and organised the attack in the way that helped to ignore the existing security system and cause significant damage to people, location, and facilities. They obviously used specific equipment. The given tragic event resulted in the death of thirty-two people. More than 300 individuals had to go to the hospital because of numerous wounds (Security Case Study n.d.).
One more terrorist act happened on June 28, 2017, in Istanbul. The Ataturk international airport was chosen as the primary aim. Terrorists used firearms and bombs (Azani, Lvovsky & Haberfeld 2016). In such a way, these tragic accidents prove that security systems used in airports today are not perfect as there are numerous problems in the organisation of security and specialists performance (Azani, Lvovsky & Haberfeld 2016).
That is why it is critical to investigate all aspects of these attacks and analyse reports of special boars created with the primary aim to eliminate vulnerabilities that resulted in the appearance of this situation. Thus, using these cases as the background for their cogitations, ICAO and other international organisations come to the conclusion that the existing measures might not suffice the emerging threats (Azani, Lvovsky & Haberfeld 2016).
At the same time, the tragic events mentioned above show terrorist organisations desire and ability to perform terror and cause serious damage to the aviation industry which remains an attractive target because of its vulnerability and numerous victims that might appear because of the crash of aircraft (Azani, Lvovsky & Haberfeld 2016). These also show the international character of the threat and the necessity of the creation of an appropriate response that will be able to consider the majority of existing problematic issues and result in their elimination (Abeyratne 2016). The importance of the problem is also evidenced by the fact that ICAO secretary general Fang Liu informed the UN and its counter-terrorism committee about the incredibly high risk of attacks and the rise of terrorism aimed at causing harm to the sphere of aviation (Moore 2016).
The increased importance of the given problem is evidenced by the fact that today terrorists tend to use diverse approaches and methods to damage aircraft and facilities. For instance, in accordance with the ICAO report, a significant diversification of devices and tools that are used by malefactors result in the increased complexity of the efficient and timely identification of threats and their elimination (Chair 2017).
In addition, ISIS and other terrorist organisations might use combined approach including cyber attacks, human factor, and diverse tools to organise an act of terror. For this reason, the sphere of civil aviation meets a significant challenge to overcome all problematic issues that emerge due to the rise of terrorism and technologies that could be used to carry out malicious actions. Under these conditions, ICAO and IATA recommendations regarding the improvement of security systems and acquire the top priority as one of the potent tools to resist threats.
International Organisations (ICAO, IATA) Recommendations and Actions to Improve Security Systems and Minimise Risks
Having outlined the basic security concerns peculiar to the sphere of civil aviation and their current state, we can now delve into the ways ICAO, IATA, and other organisations plan to improve security systems. For this reason, the given section revolves around the basic features of existing conventions, agreements, and recommendations to civil aviation globally. It also demonstrates how the given recommendations are used in real-life conditions and their effect on the existing working environment. For this reason, we review the existing literature and case studies related to the issue and create the basis for the discussion.
International Organisations (ICAO, IATA) Recommendations and Actions regarding the Human factor
As it has already been stated, ICAO and IATA have numerous concerns related to problem and threats associated with human factors. For instance, these agencies recommendations include the creation of the environment that promotes additional training and education in staff (Stewart & Mueller 2017). The latest ICAO (2017) conventions include the idea that all workers of diverse civil aviation organisations should be provided with general knowledge of human factors and their impact on performance, competence, and limits.
This information could be provided in different forms that include seminars, additional training, and stable access to sources that contain basic information about the central aspects of the problem of human factors. IATA (2017c) also admits that these measures are crucial to attain a better understanding of bulletins on human factors created by diverse aviation organisations. Additionally, IATA (2017d) points out the necessity of additional education or supervisory staff as they should have at least the basic understanding of the ways human factors might endanger the sphere and how they should be mitigated. The improved levels of education among the supervisory staff will also help to assist employees in their decision-making and attain better results. (IATA 2017b).
ICAO also recommends using in-house specialists especially in large aviation companies (ICAO traveller identification event n.d). There are several reasons for giving such recommendations. First, this sort of specialists might provide in-house expertise and capability to identify and recognise human factors and problems associated with them appropriately (ICAO traveller identification event n.d). The fact is that in accordance with research, employees who have significant experience of working in a company for a long period might suffer from decreased levels of attention and subjectivity of their judgements (International Civil Aviation Organization (ICAO) n.d.).
In other words, the overall efficiency of diverse operations and outcomes might suffer (Nensel 2017). That is why ICAO recommends using in-house specialists to attain the needed level of expertise and monitor the functioning of diverse departments. Both ICAO and IAA recommend hiring human factor consultant as one of the ways to minimise the probability of error and ensure that employees will demonstrate the high level of performance during their working hours (IATA n.d.b; Oxley 2017).
The central advantage of this approach is that human factors consultants possess deep knowledge related to the sphere, and are well-informed about education and experience (Richards 2013). That is why they might provide advice needed to improve the existing framework and attain better outcomes. In addition, their recommendations demonstrate the enhanced objectivity because of their detachment from the existing working environment, organisational pressure, and personal preference. (Smith 2018). Solutions offered by these specialists should be implemented to ensure the creation of a new secured environment (ICAO 2016; ICAO n.d.b).
Delving into this very recommendation and its implementation into the real-life setting, we might observe some alterations in the sphere promoted by ICAO and IATAs conventions on human factors. For instance, in accordance with the latest reports, diverse Western airlines (U.S. and British ones) have already benefited from the reorganisation of their functioning in terms of the newest approaches suggested by international aviation organisations (Airports Council International 2010).
Moreover, there is evidence that the staff in these states are given additional and comprehensive training at the regular basis to ensure that they remain competent and informed about new threats that emerge every day (Airports Council International 2010). This training encompasses a wide array of competences including skills needed to use diverse devices that are now an integral part of the sphere, and competencies needed to minimise the probability of a mistake caused by a human factor. (Air Line Pilots Association n.d.). Unfortunately, in some areas (Eastern Europe, some Asian states) the situation remains complex as the basic recommendations related to the improvement of this aspect are disregarded, and the staff still lacks skills and knowledge needed to create a safer environment.
Therefore, ICAO (n.d.c) also outlines a significant role motivation plays in the elimination of problems associated with human factors. In accordance with IATAs (2017) report, the given aspect remains the central issue helping to significantly reduce the number of poor mistakes in civil aviation and eliminate the negative impact of the human factor. Due to this fact, all airlines and aviation organisations accept the idea of the cultivation of motivation with the primary aim to attain its increased levels (Smith 2018).
Regarding this very goal, high salaries could be considered a potent tool to satisfy workers and impact their motivation levels (Choi & Jae 2013). At the same time, managers should be ready to encourage employees by using appropriate incentive practices and guaranteeing fair rewards (Choi & Jae 2013).
IATA (2016) also states that monitoring and provision of in-time responses become another significant concern in terms of the gradual improvement of civil aviations functioning and efficient management. The use of the innovative monitoring system can help to trace alterations in workers moods and how particular managerial decisions or solutions impact their performance levels (U.S. House of Representatives Committee on Homeland Security 2011).
Due to the use of these systems, specialists can reveal the most problematic issues related to motivation. Another important factor is that all information collected during the monitoring stage could be utilised to support the use of new methods that are accepted by employees and might really help to improve the situation (Benny 2012). IATA (2017) also recommends considering additional training another potent approach to improve the functioning of airports and minimise the number of mistakes. To meet all challenges that emerge in the modern environment, the staff should be provided with the additional training promoting new competencies and skills (IATA 2017).
The attempts to increase employee’s motivation could be observed in diverse airlines that act following ICAO and IATA recommendations (Asset value, threat/hazard, vulnerability, and risk n.d.; ICAO n.d.d). High salaries remain one of the most frequently used motivational tools as a significant rise in employees wages can be observed in the last five years (Airports Council International 2010).
Altogether, ICAO and IATA suggest similar recommendations related to the problem of the human factor. Both organisations are sure that the given threat remains topical for the modern civil aviation and should be given significant attention. At the same time, they believe that the improved competence and motivation could be considered key to the solution of the given problem as they result in the reduction in the number of mistakes that emerge under the impact of this factor and improve the overall outcomes by eliminating factors that might trigger the growth of dissatisfaction in staff (Thomas 2008). In general, these recommendations are implemented globally; however, there are still airlines (especially in Eastern and Asian regions) that still experience problems with the implementation of these recommendations.
International Organisations (ICAO, IATA) Recommendations and Actions regarding the Cyber security
As we have already stated, cyber security is another concern that remains topical today. Thus, one of the apparent solutions to the given problem is the creation of the joint approach that will help to meet new challenges and coordinate actions at the international level (ICAO 2017). Moreover, agencies insist on the improved collaboration and cooperation between international organisations and airlines.
Thus, regarding this fact, and the tendency toward the further deterioration of the situation, increase in the number of vulnerabilities, and the high need to provide effective responses to all these threats, the International Civil Aviation Organisation (ICAO), the International Coordinating Council of Aerospace Industry Associations (ICCAIA), Airports Council International (ACI), and the Civil Air Navigation Services Organisation (CANSO) decided to create a joint approach to the organisation of security measures and provision of appropriate responses to emerging cyber threats (Civil Aviation Cybersecurity Action Plan n.d.).
This Civil Aviation Cybersecurity Action Plan is now a central document regulating the terms of the international cooperation between all agencies mentioned above and cultivate the elaboration of a new environment and improvement of protective systems, approaches, tools, and methods (Civil Aviation Cybersecurity Action Plan n.d.). The given agreement should also prepare the industry against future problems that might appear due to the rise of cyber threats (Civil Aviation Cybersecurity Action Plan n.d.).
In other words, all leading international aviation organisations (ICAO, IATA, CANSO, ACI, ICCAIA) will cooperate to exchange data, experiences, visions, and perspectives on the outlined issue as it becomes the only possible way to remain efficient. They also agreed on the creation of the Roadmap as the fundamental plan that outlines future actions and goals. It includes the following points:
- elaborate a common perspective on cyber threats;
- share risk assessment;
- agree on a common language;
- outline specific recommendations;
- present to the public a new joint approach;
- promote cooperation among state-level authorities and industry to establish coordinated aviation cybersecurity policies;
- promote a robust cybersecurity culture;
- promote the use of current security measures;
- establish mechanisms to share information;
- ensure situational awareness;
- refine best practices (Civil Aviation Cybersecurity Action Plan n.d., pp. 2-3).
This plan shows all activities that might be needed to achieve success and reorganise civil aviation to guarantee its better work. At the very beginning, ICAO, IATA, CANSO, ACI, and ICCAIA show the need for the elaboration of a joint approach to work with cyberthreats which is also considered the background for the improved collaboration between all these agencies (Civil Aviation Cybersecurity Action Plan n.d).
It is essential that all parties should have a similar understanding of the situation and how it will evolve in several years. Only under these conditions, they will be able to work together and contribute to the gradual improvement of the situation in the sphere (ICAO 2016). The given idea acquires the top priority as organisations like ICAO or IATA precondition the further development of the sphere and its ability to cope with all challenges that emerge (Civil Aviation Cybersecurity Action Plan n.d.).
This cooperation at the international level will also facilitate risk assessment procedures and increase the level of awareness to elaborate more effective security measures. ICAO, IATA, CANSO, ACI, and ICCAIA also promote the cultivation of shared risk practices to help airlines discover and address existing problematic issues peculiar to this field (A framework for aviation cybersecurity 2013). Today, there is a plenty of approaches utilised by companies and agencies to identify aims of attacks and their consequences (Tamasi & Demichela 2011). They use different sets of data and might devote attention to multiple aspects of incidents.
It is apparent that the given divergences undermine the efficiency of cooperation and might result in the appearance of multiple loopholes in security systems (Tamasi & Demichela 2011). That is why one of the central aspects of the given plan is the creation of the background needed to share experiences and elaborate common approaches to risk assessment (Civil Aviation Cybersecurity Action Plan n.d.). The adherence to this approach will help to attain the improved ability to assess all risks and provide appropriate responses to them by using the joint approach (Singer & Friedman 2014). It will also help to increase awareness of less efficient or smaller agencies as they will have an opportunity to investigate a collective experience of diverse agencies.
The plan created by companies also emphasises the need for “joint prepositions and recommendations” (Civil Aviation Cybersecurity Action Plan n.d., p. 2). In other words, all parties to the agreement are ready to determine the central areas that need improvement and provide their recommendations required to eliminate all vulnerabilities and create a new safer environment (Abeyratne 2016).
These offerings could also be considered guides for airlines that try to improve their functioning. In general, the given approach turns out to be a potent tool that can be used to reorganise the work of civil aviation and attain better outcomes (Abeyratne 2016). Utilising the shared risk assessment practice, specialists will be able to cultivate a new setting deprived of multiple problematic issues already known to organisations like ICAO and IATA (ICAO 2016). Processing new sets of data, companies will also improve their functioning and outcomes.
Another step needed to ensure security to passengers and workers is the creation and implementation of a robust cybersecurity system and culture (Civil Aviation Cybersecurity Action Plan n.d.). The fact is that every day we might observe the emergence of new potential threats and methods to cause damage to security systems which means that elaboration of a completely new security culture remains the only option to preserve the stable functioning of the sphere (Abeyratne 2016).
For this reason, all parties participating in the agreement mentioned above help companies in implementing and improving their strategies that are used protect software from maleficent actions and terrorist attacks (Abeyratne 2016). This assistance also helps to cultivate a completely new culture mentioned above and needed to attain better security levels, minimise the probability of hackers attacks, terrorist acts, and guarantee the stable functioning of airports.
All organisations also admit the high need for efficient mechanisms of data sharing and transfer as the central component of the security measures development (A framework for aviation cybersecurity 2013). The given tool is essential for the further development of the field as diverse companies face multiple problems in their functioning and generate precious experiences that can later be used by other companies in similar situations (ICAO n.d.c.). In the globalised world, the use of the joint approach becomes the only possible way to resist pressure and terrorism. That is why the existence of the efficient data sharing mechanism will simplify the task and help to attain enhanced collaboration between diverse agencies across the globe (IATA 2017a).
Situational awareness is another element of Civil Aviation Cybersecurity Action Plan that plays a central role in the creation of a safer environment (ICAO 2017). It preconditions the constant exchange of information between companies and agencies for them to remain informed about the most important issues and problems peculiar to the sphere (Civil Aviation Cybersecurity Action Plan n.d.). It turns out to be an efficient approach facilitating the collaboration and providing opportunities for better coordination of actions between ICAO, IATA, and other international organisations.
At the moment, the majority of these recommendations are observed by airlines across the globe. Correctly realising the necessity and importance of the joint approach, companies adhere to the basic regulations suggested by ICAO, IATA, and other international agencies. Besides, in accordance with the latest statistics, despite the tendency towards the emergence of new threats, the high level of cyber security and decrease in successful hackers attacks could be observed (IATA 2017). It might be achieved due to the constant sharing of data between airlines and the cultivation of the joint approach that minimises the risk of intrusion and provides security specialists with new opportunities for the detection and elimination of potential cyber threats.
International Organisations (ICAO, IATA) Recommendations Actions Regarding the Terrorism
As we have previously stated in the paper, the risk of terrorist attacks remains high. For this reason, ICAO and IATA recommend the use of specific security systems, tools, and approaches to minimise the probability of the attack and provide passengers with the safe environment. That is why in accordance with international organisations conventions, the majority of airports, especially in areas characterised by the high risk of terrorist activity, several lines of defence are introduced (Aviation terrorism n.d.). These lines can guarantee safety to all facilities, like landing zone, terminals, fuel storages, etc. (Aviation terrorism n.d.).
The existence of several lines also helps to eliminate loopholes and minimise the risk of intrusion because of the multidimensional approach to the organisation of securing in airports. Furthermore, Furthermore, ICAO (2017) says that the use of the innovative and powerful software will obviously help to improve digital security and ensure stable functioning of an airport. The in-depth investigation of existing vulnerabilities and monitoring of individuals performance g should be supported by metal detectors, X-ray scanners, etc. (Alexander & Hyland 2016).
Moreover, investigating the functioning of modern airports, the wide use of innovative technologies could be admitted. First, to avoid the appearance of explosive bombs and other dangerous objects on board, all baggage is x-rayed with the help of specific devices (Alexander & Hyland 2016).
It helps to remain informed about things carried by passengers and reduce the risk of terrorist attacks. All airports are equipped with metal detectors that are also considered primary security tools. Individuals who use civil aviations services have to pass through these detectors to ensure security officers that no prohibited objects are present. (Hoton 2012). These measures could be considered regarding the Chicago Convention stating that all passengers and their baggage should be scanned to reduce the risk of malicious action and provide security guarantees to all individuals during the flight (ICAO 2016).
However, the rapid development of technologies and emergence of new ways to cause damage to people, aircraft, and facilities deteriorate the efficiency of these measures which means that the introduction of additional checks and devices is demanded (Hoton 2012). Organisations like ICAO and IATA also recognise the gradual rise in the complexity of tools used to perform terrorist attacks. For this reason, they recommend using the combined approach that presupposes the use of metal detectors, X-ray scanners, and canines to accomplish the task and ensure that no harmful substances or other potentially hazardous objects are present (Aviation terrorism n.d.).
In such a way, regarding the high sophistication of terrorist attacks, the corresponding diversification of security systems might be considered the only possible response. ICAO and IATA (2017; 2017a) recommend the creation of innovative and multidimensional security systems that will be able to discover potential threats and eliminate them before accidents.
In addition, the trained staff remains a central aspect of the efficient security system of the 21st century. That is why international aviation organisations outline the necessity of additional training and education for employees as they should be able to participate in the majority of security actions and guarantee the maintenance of the safe environment in airports (Kaplan 2017). The report related to the issue shows that in UK, USA, Germany, and France, the level of workers preparedness remains high which means that the ICAOs conventions are observed (United Kingdom Government 2010). At the same time, there are still numerous problematic issues that emerge due to the deterioration of the international relations and spread of terrorism. That is why all airports should remain engaged in the continuous improvement process.
Regarding conventions on airport security and ICAO recommendations, the staff at all international airports should undergo background checks. There are several reasons for this procedure. First, it is demanded to ensure that a would-be worker is not a criminal and his/her intention to work in the civil aviation sphere is not precondition by some inappropriate motifs (Hoffman 2017). Second, the latest accidents related to cyber attacks show that hackers might be found among members of the staff. For this reason, these checks might also help to discover potential malefactors and prevent them from causing damage to all systems.
There is another, more important reason for background checks. In accordance with diverse security agencies reports, terrorists might use so-called sleeping agents to perform terrorist acts. (Horizon Intelligence n.d). These individuals work in airports as usual employees; however, they might assist malefactors in their attempts to break security systems and interfere with the functioning of airports. (Hoton 2012).
Moreover, they can perform terrorist acts on their own. Under these conditions, background checks become fundamental for the provision of a safe environment both for workers of airports and passengers. Unfortunately, there are numerous errors in the implementation of these checks and their accomplishment. As a result, diverse individuals remain unrecognised and might work in the sphere of civil aviation during long periods of time enough to prepare terrorist acts and perform them.
Risk assessment and problem definition become potent tools that could also be used to eliminate the threat as a specialist using this approach might find a problem in the current security system and insist on using a specific tool to solve it.
In general, the current situation in civil aviation regarding the growing terrorist threat could be described as dangerous one. The fact is that the majority of tools that are used today cannot guarantee complete and ideal protection from all threats that exist at the moment (Johansen 2017). That is why both ICAO and IATA, as well as other international organisations, insist on elaborating a joint approach to the aviation security.
Unfortunately, so far not all states have implemented the basic suggestions of conventions on aviation security (Mackenzie 2010). It means that there are still numerous vulnerabilities that can be used by malefactors with the primary aim to cause damage to aircraft and facilities and injure people. In this regard, we might admit numerous efforts to promote the further spread of the joint approach and robust security systems with the primary aim to minimise the probability of maleficent actions and create a new safer environment for passengers (Fanke 2016).
At the moment, multiple airlines in USA, UK, and Europe prefer to adhere to the basic recommendations provided in conventions by ICAO and IATA (Aviation terrorism n.d.). It results in their more efficient functioning and reduction in the number of accidents. However, these states also belong to a particular risk group which means that new attempts to perform terrorist acts might be observed in future. This fact emphasises the necessity of the further cultivation of security systems and their diversification with the primary aim to resist emerging threats effectively. Only under these conditions, some positive result could be achieved.
Conclusion
Altogether, the given literature review perfectly demonstrates the existence of numerous threats to the civil aviation and its security. The sources were used to answer research questions formulated at the beginning of the document. Furthermore, assessing data from this review, we will be able to choose methods that fit the purpose of our research and help to reveal all issues that might be associated with this very investigation. At the same time, the given section creates the basis for the further discussion of the central problem and existing threats to the security. Finally, the literature review section is critical for making appropriate conclusions provided at the end of the document.
Methodology
Introduction
In the given section, the in-depth and comprehensive description of methods chosen to research the given issue and analyse essential information is offered. Additionally, we provide the theoretical rationale for selecting specific approaches to evaluate information and provide a credible conclusion. Correctly realising a unique significance of the given element of any research, we describe how the chosen methods are applied to the real-life condition and how the study is conducted.
Explanation of the Mixed Approach
Regarding the nature and central goal of our research, we explore mixed method. It means that to investigate the problem outlined in the previous sections and answer research questions, we collect both qualitative and quantitative data. The necessity of the given approach is explained by the diversity of threats, their complex impact on the sphere of civil aviation, and multiple agents affected by these concerns. Qualitative data collected for the research might include subjective judgements and individual perspectives on the outlined threats. For this reason, it is not measured; though it is provided for the discussion.
As for the quantitative data, it is measured using methods outlined in specific recommendations for research projects. The advantageous character of this approach is proven by the fact that the most powerful aspects of both qualitative and quantitative methodologies are incorporated within a single study to attain the best possible results (American Psychological Association 2010). the convergence of findings and information acquired using both these measures will increase the credibility of findings and prove the relevance of conclusions (Walter & Andersen 2013).
Data Collection Procedure
As far as we use the mixed approach to investigate the issue and provide credible information about it, the necessity to explore diverse data collection methods becomes apparent (Yin 2017). It is critical to ensure that the project utilises multiple sources like dissertations, observations, theories, case studies, governmental reports to create the theoretical background for the investigation and organise these findings in an efficient and understandable manner (Adams & Lawrence 2018).
For this reason, the first method is the literature review that is essential for the research project as it provides the existing perspective on the investigated issue and outlines all problematic conceptions that should be touched upon in the research (Trochim 2016). In the study, we explore both primary and secondary sources which mean that governmental reports, ICAO and IATA conventions, as well as books, peer-reviewed articles, and credible websites are used. Primary sources contribute to the improved understanding of the roots of the problem and specialists perspectives on it (Yin 2017). From another hand, secondary sources help to discuss, analyse, and implement data provided by primary sources (Yin 2017).
The given approach helps to fill in the gaps in knowledge about the issue and conduct the in-depth study. The section of the literature review contains statistical data regarding the emergence of threats and incidents. It demonstrates current tendencies in the sphere of aviation and how often some problems emerge due to various factors (Creswell 2014). We collected data from aviation companies’ reports, their websites, and other sources related to the appearance of potential threats and their further evolution. Numerous graphs are also offered to demonstrate the rise of the problem and its monitoring.
Another method utilised in the paper is a specially designed questionnaire. It is distributed among employees who have been working in the sphere of civil aviation for 5 and more years. The primary aim of this interview is to collect these individuals perspectives on the current state of security systems, their efficiency and ability to suffice new demands to safety. The interviewees were asked about the efficacy of measures, recommendations, and conventions suggested by ICAO, IATA, and other agencies. They had to provide their vision of changes and their efficiency regarding the elimination of emerging threats.
Questionnaire
The designed questionnaire contains ten basic questions:
- What threats do you consider the most topical regarding the current state of civil aviation?
- What is your perspective on the organisation of security measures?
- Do you agree with the recommendations and conventions suggested by ICAO, IATA, and other international organisations?
- Do you notice positive changes attained due to the implementation of these recommendations?
- Do you agree that there is a tendency towards the gradual increase in the efficiency of the suggested security measures?
- Do you feel safe working in the given sphere? Do these feelings result from ICAO and IATAs efforts?
- Have you noticed a decrease in the number of accidents?
- What negative tendencies can you admit?
- Are modern security measures more efficient if to compare with previous ones?
- What do you think about ICAO and IATAs conventions and measures? Are they central to the creation of a new safe environment?
The introduction of these questions is preconditioned by several factors. First, they are clear and understandable which means that participants will have no problems with their comprehension and will be able to answer all of them. Second, they will collect personal data needed to conclude about the efficiency of ICAO and IATAs recommendations and their impact on the functioning of civil aviation. For this reason, the given questionnaire is considered an appropriate tool to investigate the suggested research issue.
Sampling Procedure
Fifty employees working in the sphere of civil aviation were chosen for the research. The target population for the study includes individuals with five and more years of experience in the field. It is needed to evaluate experiences peculiar to this very group and their attitudes to events occurring in the sphere of aviation. The gender, age, social or cultural status were disregarded as they are not significant for the investigation. For this reason, simple random sampling method was chosen as the most appropriate approach to conduct the needed investigation (Yin 2017). All individuals who with the needed qualities had the equal opportunity to participate in the research and provide their perspectives on the researched issue.
Ethical Concerns
Regarding the nature of the research and involvement of individuals to acquire relevant data and statistics, specific ethical concerns should be considered. It is central to the credibility of the research and its ability to meet all demands to research projects of this sort.
First, as it is required by diverse organisations monitoring the quality of studies, all participants were explained the basis of the project, its nature, basic features, purposes, and outcomes (Adams & Lawrence 2018). This stage is essential for the acquisition of individuals informed consent to participate in the research and provide their perspectives on one or another point under the investigation. It ensures that no problems because of misunderstanding will appear during diverse stages of the project (Adams & Lawrence 2018).
Second, the participation was voluntary. It means that all workers chosen for the interview had an opportunity to refuse because of their personal motifs, lack of time, or absence of the desire (Yin 2017). It is a critical aspect of any project as forced consent will obviously violate the basic ethical principles and result in the corruption of data acquired in the course of a study.
Third, all interviewees were guaranteed confidentiality and complete anonymity of data provided by them. The given aspect contributes to the enhanced credibility of findings as participants do not experience stress and become an opportunity to provide credible and relevant information about the current state of the investigated issue (Adams & Lawrence 2018). For this reason, no real names or some other personal information was used.
Finally, participants are provided with an opportunity to ask for the copy of the research paper to ensure that their answers are not corrupted and are presented appropriately. These basic aspects ensure observation of the basic ethical principles and guarantee the enhanced credibility of findings. Additionally, they are necessary for the improved outcomes.
Analysis of Findings
The analysis of the results of the survey is critical for the project. For this reason, all answers were evaluated regarding their positive and negative feedbacks about the efficiency of measures and alterations the respondents have been noticing during the latest years. Therefore, 43 interviewees admitted numerous positive changes that happened under the impact of ICAO and IATA conventions.
They agreed that there is the tendency towards the further improvement of security measures and that these agencies play a central role in the creation of a new safer environment. 38 respondents also outlined the fact that they feel safe in their workplace due to the efficient implementation of these conventions. 47 individuals admit the rise of terrorism and cyber threat as the negative tendencies; however, they are sure that ICAO and IATA s recommendation will help to mitigate these factors negative impact on civil aviation. 45 interviewees consider the further elaboration of the joint approach to security the only possible solution (see Figure 10 in Appendix).
Altogether, the reviewed literature was applied to these survey findings to analyse respondents answers and admit the latest alterations in the sphere of civil aviation. In such a way, we compare results of qualitative and quantitative approaches to observe if there is a convergence of data which can prove the existence of positive alterations in civil aviation under the impact of ICAO and IATA conventions. It is a central aspect of the paper.
Findings
Threats to Civil Aviation, ICAO and IATAs Responses
Analysing data acquired during the research, we come to the conclusion that civil aviation faces the three significant threats nowadays. These are the cyber threat, terrorist attacks, and problems associated with the human factor. For this reason, international aviation organisations like IATA and ICAO introduce specific measures to investigate these dangers and guarantee the creation of a safe environment that will be able to meet all requirements and satisfy both workers and passengers.
Therefore, elaboration of The Civil Aviation Cybersecurity Action Plan and creation of numerous conventions that include recommendations for companies and security specialists become the efficient measures in struggling against these threats and mitigating their adverse effects on the whole sphere. Both ICAO and IATA correctly realise the necessity of the further evolution of security measures.
In this regard, organisations insist on the introduction of a joint approach that will become an appropriate measure in identification and elimination of these threats. The majority of airlines that observe these recommendations demonstrate the decreased risk of being attacked and improved functioning. For this reason, measures suggested by ICAO and IATA become a potent tool to struggle against all forms of terrorism and enhance the work of the staff to minimise the risk of mistakes or appearance of emergent situations.
Interview
As it has already been stated, 50 individuals participated in the research. All they provided their informed consent and provided credible data about the investigated issue. Thus, the majority of interviewees agreed that terrorism and cyber attacks are the central threats to civil aviation today. However, only 27 individuals recognised the human factor as another problem.
It evidences the lack of knowledge about the issue. Nevertheless, the bigger part of respondents (45) was sure that the creation of a joint approach is an efficient measure that will help to reduce the level of threat and avoid complications in future.45 employees also demonstrated their readiness to follow these recommendations because of their efficiency and positive impact on the development of security measures. At the same time, the majority of participants admitted numerous positive changes that occurred in civil aviation during the last years. These include better security measures, improved working conditions, and overall progress regarding the organisation of work and provision of services. 45 respondents associate it with the activity of ICAO and IATA.
Nevertheless, 43 interviewees noticed that there were numerous positive tendencies towards the further increase in the efficiency of measures suggested to eliminate existing threats and establish a new more protected environment. At the same time, only a few individuals participating in the research state that the functioning of airports and airlines might become worse under the impact of ICAO and IATAs conventions.
The given fact proves the increased efficiency of these recommendations and their clear and understandable character as they are accepted by the majority of employees working in the sphere. Comparing the previous and modern approaches to the organisation of security and elimination of threats, respondents notice that there is the obvious progress and today, the efficiency of security systems remains at the high level (45 respondents).
Another important aspect is that the bigger part of all respondents feels safe at their workplaces which could be considered a significant achievement of organisations responsible for the provision of security guarantees to workers. The majority agrees that ICAO and IATA play central roles in the creation and promotion of a new environment that will help airlines to improve security measures and avoid the emergence of problematic issues.
In general, results of the given survey prove the efficiency of ICAO and IATA regulations aimed at the improvement of the situation in civil aviation and creation of a new environment free from the threats mentioned above. The give results could be used in the discussion session. The data can be seen in Figure 10 in Appendix.
Discussion
In such a way, we can use data acquired during the research to answer the formulated research questions. Speaking about the first one, we can now state that the introduction of ICAO and IATA recommendations apparently contributes to the creation of a new safer environment and minimising of the level of threat. It is evidenced by numerous sources that revolve around the issue and provide facts proving this assumption. Additionally, data collected via the interview with employees shows that the majority of workers admit the reduction of problematic concerns and appearance of a new environment characterised by the absence of real threats to their functioning and passengers lives. Statistical data also proves a significant improvement in the sphere.
Regarding the second research question, we should also report numerous alterations in approaches to security under the impact of ICAO and IATA conventions. The fact is that old security systems were not able to meet new requirements, guarantee safety to passengers, discover and eliminate all threats. For this reason, these organisations conventions outlined new vectors for the development of the sphere and contributed to the implementation of new approaches to security.
The majority of modern airlines cooperate with ICAO and IATA to share data and acquire the most relevant information about the current trends in the sphere of aviation security and how it should be organised regarding the peculiarities of the emerging threats. That is why their functioning become altered under the impact of these organisations conventions and recommendations.
Revolving around the third research questions, we might use data acquired due to the use of a specific questionnaire. Evaluating the results of the interview, we can come to the conclusion that the bigger part of workers find ICAO and IATAs recommendations appropriate and admit numerous positive alterations that appear due to these very conventions. Employees demonstrate good knowledge of the basic threats that might deteriorate the functioning of the sphere at the moment. That is why they correctly realise the necessity of change to remain efficient and cope with new dangers that appear every day under the impact of diverse factors. Moreover, the survey demonstrates that workers agree that the joint approach promoted by ICAO and IATA should become the most efficient measure to struggle against new problematic issues.
Finally, we in the course of the research, we admit numerous shifts towards the cultivation of a new safer environment deprived of loopholes and problematic issues. However, it is still too early to speak about the full transformation under the impact of ICAO and IATAs conventions. The fact is that there are still numerous vulnerabilities and weaknesses in existing security systems that might be used by malefactors.
In such a way, results of the literature review and questionnaire prove significant alterations in civil aviation and security. The appearance of new threats resulted in drastic changes in methods and approaches. For this reason, nowadays a shift towards the joint approach under the impact of new conventions could be noticed. Its efficiency is evidenced by employees attitudes and perspectives on recommendations and significant improvement of the functioning of civil aviation.
Conclusion and Recommendations
In conclusion, data from literature review, statistics related to civil aviation, and employees perspectives on the problem prove that ICAO and IATAs conventions remain a potent tool in struggling against the three threats to the aviation security. This data evidences that these organisations are successful in the creation of a new environment and improving the existing security systems. Moreover, these recommendations help to monitor the current state of these issues and introduce appropriate responses to the emerging threats. Unfortunately, sometimes these recommendations are disregarded which results in poor outcomes.
Nevertheless, the questionnaire demonstrates that the conventions help to align the efficient functioning of diverse airlines and provide safety to passengers. However, the complete elimination of threats becomes possible only regarding the improvement in the global relations and elimination of terrorism. Till that time, it is critical to preserve ICAO and IATAs recommendations.
Appendices
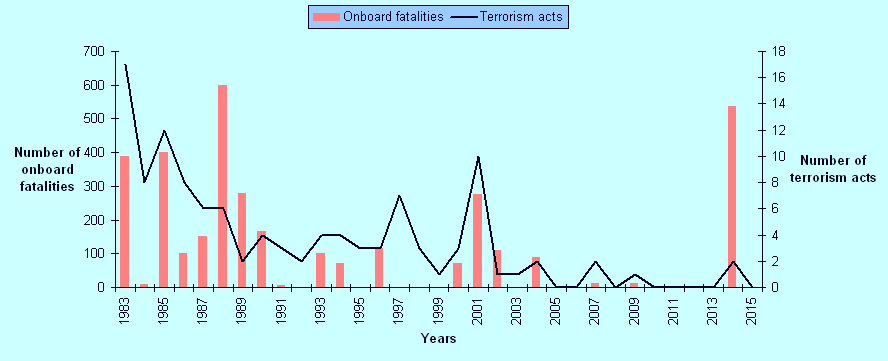
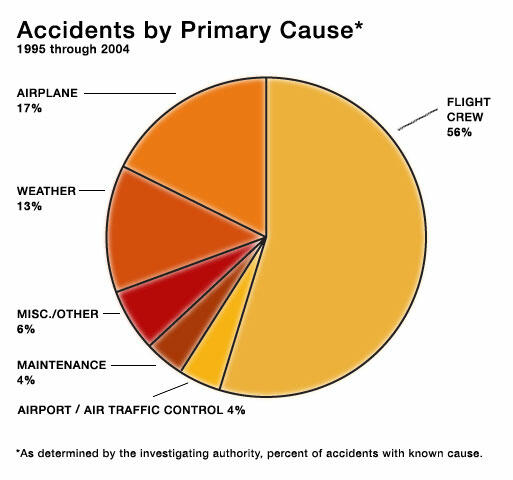
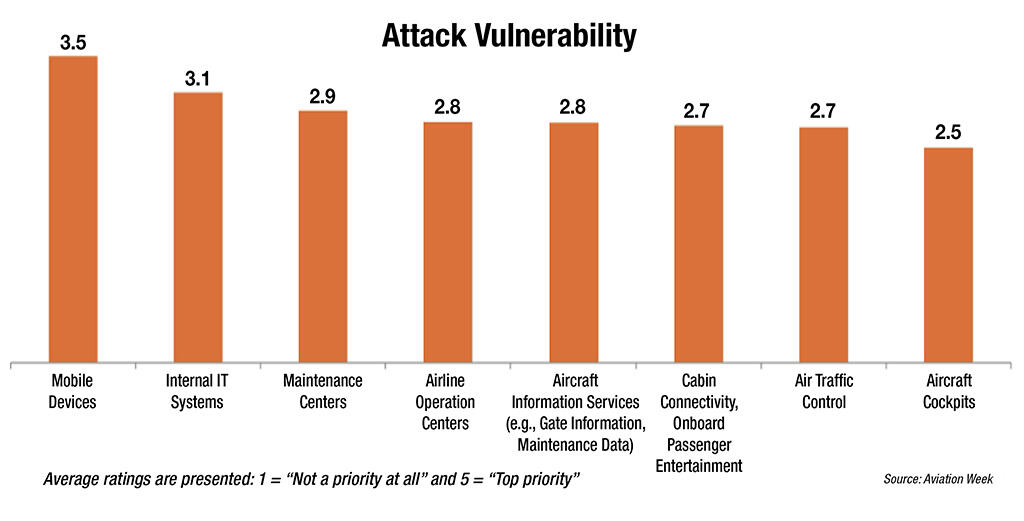
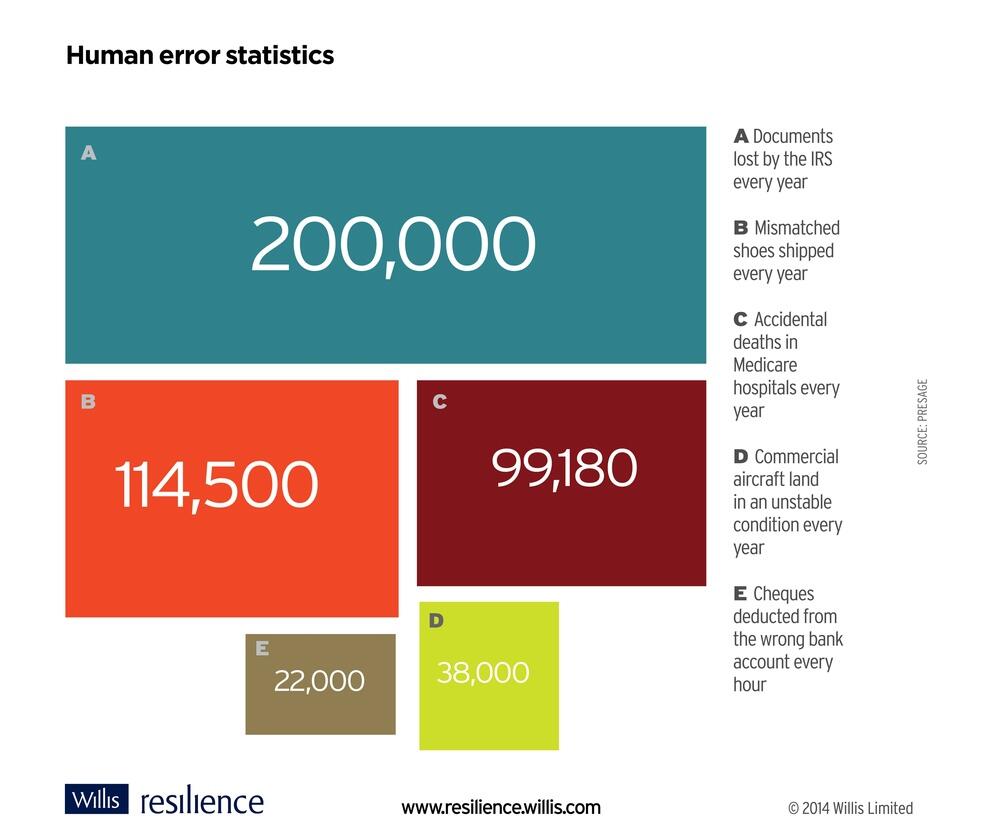
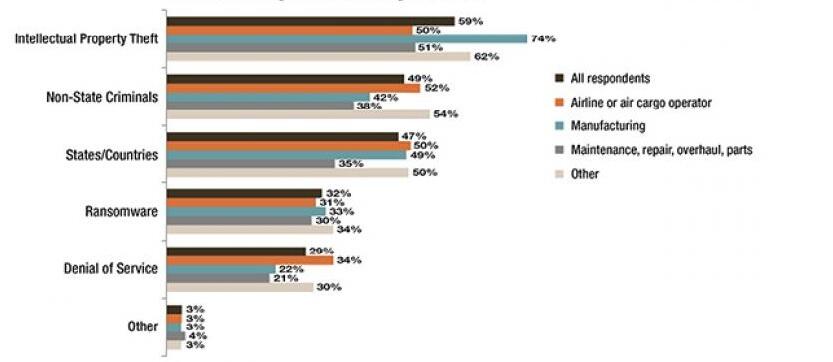
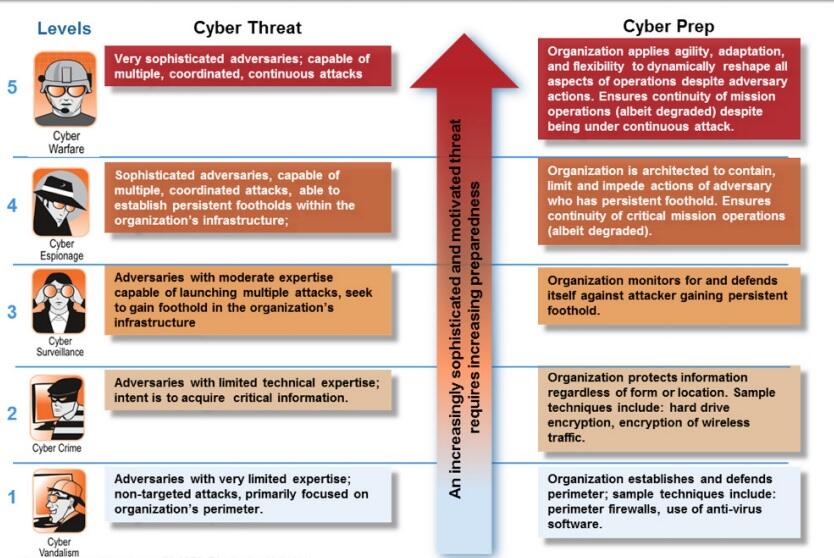
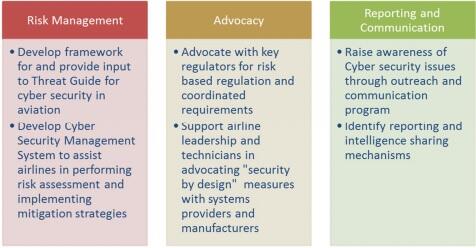
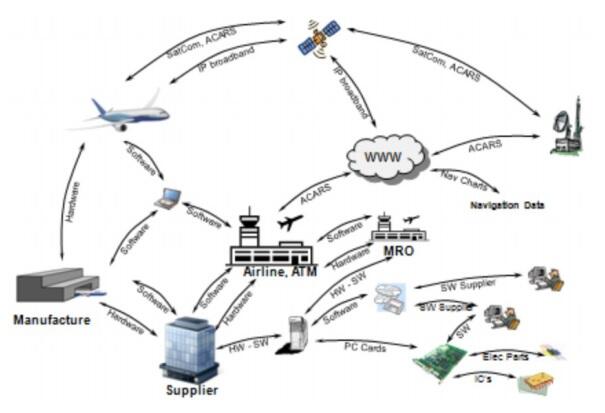
References
A framework for aviation cybersecurity 2013. Web.
Abeyratne, R 2016, Rulemaking in air transport, Springer, Montreal.
Adams, K & Lawrence, E 2018, Research methods, statistics, and applications, SAGE Publications, Thousand Oaks. CA.
Alexander, D & Hyland, A 2016, ‘Expecting the unexpected in aviation terrorism’, Security. Web.
Arasly, J 2005, ‘Terrorism and civil aviation security: problems and trends‘, The Quarterly Journal, pp. 75-102. Web.
Air Line Pilots Association n.d., Aviation security: 10 years after the 9/11 attacks. Web.
Airports Council International 2010, Strict regulations lead to increased focus on airport security training. Web.
American Psychological Association 2010, Ethical principles of psychologists and code of conduct. Web.
Asset value, threat/hazard, vulnerability, and risk n.d. Web.
Aviation terrorism n.d. Web.
Azani, E, Lvovsky, L & Haberfeld, D 2016, Trends in aviation terrorism. Web.
Benny, D 2012, General aviation security: aircraft, hangars, fixed-base operations, flight schools, and airports, CRC Press, Boca Raton, FL.
Caldwell, J 2012, ‘Crew schedules, sleep deprivation, and aviation performance’, Current Directions in Psychological Science, vol. 21, no. 2, pp. 85-89. Web.
CANSO 2014, CANSO Cyber security and risk assessment guide. Web.
CASA 2012, Safety risk management. Web.
Center for International Law 2012, 2010 Convention on the Suppression of Unlawful Acts Relating to International Civil Aviation. Web.
Chair, A 2017, Security Council briefing on “Terrorist Threats to Civil Aviation”. Web.
Chitty, A 2013, Civil aviation remains watchful on cyber security. Web.
Choi, H & Jae, H 2013, ‘A study on the aviation security profiling in the U.S.’, Journal of International Area Studies, vol. 16, no. 311. Web.
Civil Aviation Cybersecurity Action Plan n.d. Web.
Convention on International Civil Aviation done at Chicago on the 7th day of December 1944. n.d. Web.
Counter-Terrorism Committee Executive Directorate (CTED) 2017, Special meeting of the Counter-Terrorism Committee on “Terrorist threats to civil aviation”. Web.
Creswell, J 2014, Research design: qualitative, quantitative and mixed methods approaches, SAGE Publications, Thousand Oaks, CA.
Crevits, I, Labour, M, & Vanderhaegen, F 2014, Integrating Human factors in airport security checkpoints: a decision aiding analysis of structural incoherencies. Web.
Cromie, S, Ross, D, Corrigan, S, Liston, P, Darragh, L, & Demosthenous, E 2015, ‘Integrating human factors training into safety management and risk management: a case study from aviation maintenance’, Proceedings of the Institution of Mechanical Engineers, Part O: Journal of Risk and Reliability, vol. 229, no. 3, pp. 266-274.
Demosthenous, V 2007, Human Factors in aviation security. Web.
Dijbo, B 2012, Aviation Security. Web.
Drury, I & Shipman, T 2010, ‘Our no.1 threat: cyber terrorists who can knock a jet out of the sky‘, Daily Mail. Web.
Duchamp, H, Bayram, I & Korhan, R 2016, Cyber-security, a new challenge for the aviation and automotive industries. Web.
Elias, B 2009, Airport and aviation security: U.S. policy and strategy in the age of global terrorism, Auerbach Publications, Boca Raton, FL.
Enerstvedt, O 2017, Aviation security, privacy, data protection and other human rights: technologies and legal principles (law, governance and technology series), Springer, New York, NY.
Esposito, R, Winderm, R & Winter, T 2014, ‘ISIS terror threat to US targets ‘high,’ say officials‘, NBC News. Web.
Fanke, D 2016, Cyber security basics: protect your organization by applying the fundamentals, CreateSpace Independent Publishing Platform, New York, NY.
Ferguson, M & Nelson, S 2013, Aviation safety: a balanced industry approach, Delmar Cengage Learning, Clifton Part, NY.
Hall, R 2015, The transparent traveller: the performance and culture of airport security, Duke University Press Books, Durham, NC.
Hancock, P & Hart, G 2002, What can human factors/ergonomics offer?. Web.
Hoffman, B 2017, The terrorist threat to aviation: back again. Web.
Horizon Intelligence n.d., Terrorism and civil aviation security. Web.
Hoton, E 2012, Aviation terrorism insurance – not just for airlines!. Web.
IATA n.d.a, Aviation security. Web.
IATA n.d.b, Fact sheet. Cyber security. Web.
IATA 2016, Closer collaboration with governments to tackle threat of terrorism. Web.
IATA 2017a, Collaboration key to aviation security efforts. Web.
IATA 2017b, Estimating the impact of recent terrorist attacks in Western Europe. Web.
IATA 2017c, Future of the airline industry 2035. Web.
IATA 2017d, Safety report. Web.
ICAO n.d.a, About ICAO. Web.
ICAO n.d.b, The ICAO aviation security programme. Web.
ICAO n.d.c, Risk context statement. Web.
ICAO n.d.d, Security. Web.
ICAO 2016, Safety report. Web.
ICAO 2017, ICAO Secretary General addressed the UN Counter Terrorism Committee Special Meeting on terrorist threats to international civil aviation 2017. Web.
ICAO: fundamental human factors concepts n.d. Web.
ICAO: human factors documents n.d. Web.
ICAO traveller identification event highlights key aviation role in combatting terrorism and cross-border crime n.d. Web.
International Civil Aviation Organization (ICAO) n.d. Web.
Johansen, G 2017, Digital forensics and incident response: a practical guide to deploying digital forensic techniques in response to cyber security incidents, Packt Publishing, Birmingham.
Kaplan, F 2017, Dark Territory: the secret history of cyber war, Simon & Schuster, New York, NY.
Krause, S 2003, Aircraft Safety: accident investigations, analyses, & applications, McGraw-Hill Education, New York, NY.
Lawrence, D (ed) 2017, Aviation and airport security: management, improvement strategies and future challenges (transportation issues, policies and r&d), Nova Science Pub Inc, New York, NY.
Mackenzie, D 2010, ICAO, University of Toronto Press, Toronto.
Moores, V 2017, ICAO: Terrorism and cyberattacks are a ‘significant concern’. Web.
Nensel, M 2017, ‘IATA: terror attacks cost European airlines $2.5 billion in revenue’, ATW. Web.
Oxley, D 2017, Estimating the impact of recent terrorist attacks in Western Europe. Web.
Price, J 2013, Practical aviation security, second edition: predicting and preventing future threats (Butterworth-Heinemann homeland security), Butterworth-Heinemann, New York, NY.
Price, J & Forrest, J 2016, Practical aviation security, third edition: predicting and preventing future threats, Butterworth-Heinemann, Cambridge, MA.
Rankin, W 2010, ‘General aviation security: a safety management system model for collegiate learning’, Journal of Aviation/Aerospace Education & Research, vol. 19, no. 2, pp. 35-44. Web.
Raphael, R 2013, Airport security: a national security challenge, German Marshall Fund, Washington, DC.
Richards, A 2013. Transportation security administration’s aviation channeling services provider project. Web.
Schwaninger, A 2006, Airport security human factors: from the weakest to the strongest link in airport security screening. Web.
Security Case Study n.d. Web.
Security guidelines for general aviation airports n.d. Web.
Shay, L 2016, Ranking commercial aviation’s cybersecurity priorities. Web.
Singer, P & Friedman, A 2014, Cybersecurity and cyberwar: what everyone needs to know, Oxford University Press, Oxford.
Smith, C 2018, 4 threats to aviation security – Iata. Web.
Statistic analysis of airplane accidents n.d. Web.
Stewart, M & Mueller, J 2017, Are we safe enough?: measuring and assessing aviation security, Elsevier, Cambridge, MA.
Sweet, K 2008, Aviation and airport security: terrorism and safety concerns, Second Edition, CRC Press, Boca Raton, FL.
Tamasi, G & Demichela, M 2011, ‘Risk assessment techniques for civil aviation security’, Reliability Engineering & System Safety, vol. 96, pp. 593-599.
Thomas, A 2008, Aviation security management, Praeger, London.
Trochim, W 2016, Research methods: the essential knowledge, CI, New York, NY.
Types of sampling n.d. Web.
United Kingdom Government 2010, The United Kingdom’s strategy for countering chemical, biological, radiological and nuclear (CBRN) terrorism. Web.
U.S. House of Representatives Committee on Homeland Security 2011, Ten years after 9/11: assessing airport security and preventing a future terrorist attack, CreateSpace Independent Publishing Platform, Washington, DC.
Walter, M & Andersen, C 2013, Indigenous statistics: a quantitative research methodology, Routledge, New York, NY.
Yeh, M, Swider, C, Abbott, K, Donovan, C, Neiderman, E & Piccione, D 2012, ‘Human factors at the federal aviation administration (FAA): from research to reality’, Proceedings of the Human Factors and Ergonomics Society Annual Meeting, vol, 56, no. 1, pp. 56-60. Web.
Yin, R 2017, Case study research and applications: design and methods, SAGE Publications, Thousand Oaks, CA.
Yool, J 2005, A legal analysis of aviation security under the international legal regime. Web.
Zan, T, dAmore, F & Di Camillo, F 2015, ‘The defence of civilian air traffic systems from cyber threats‘, Instituto Affari Internazionali, vol. 15, no. 23e, pp. 1-67. Web.
Whitehead, T 2014, ‘Britain facing ‘greatest terrorist threat’ in history‘, The Telegraph. Web.